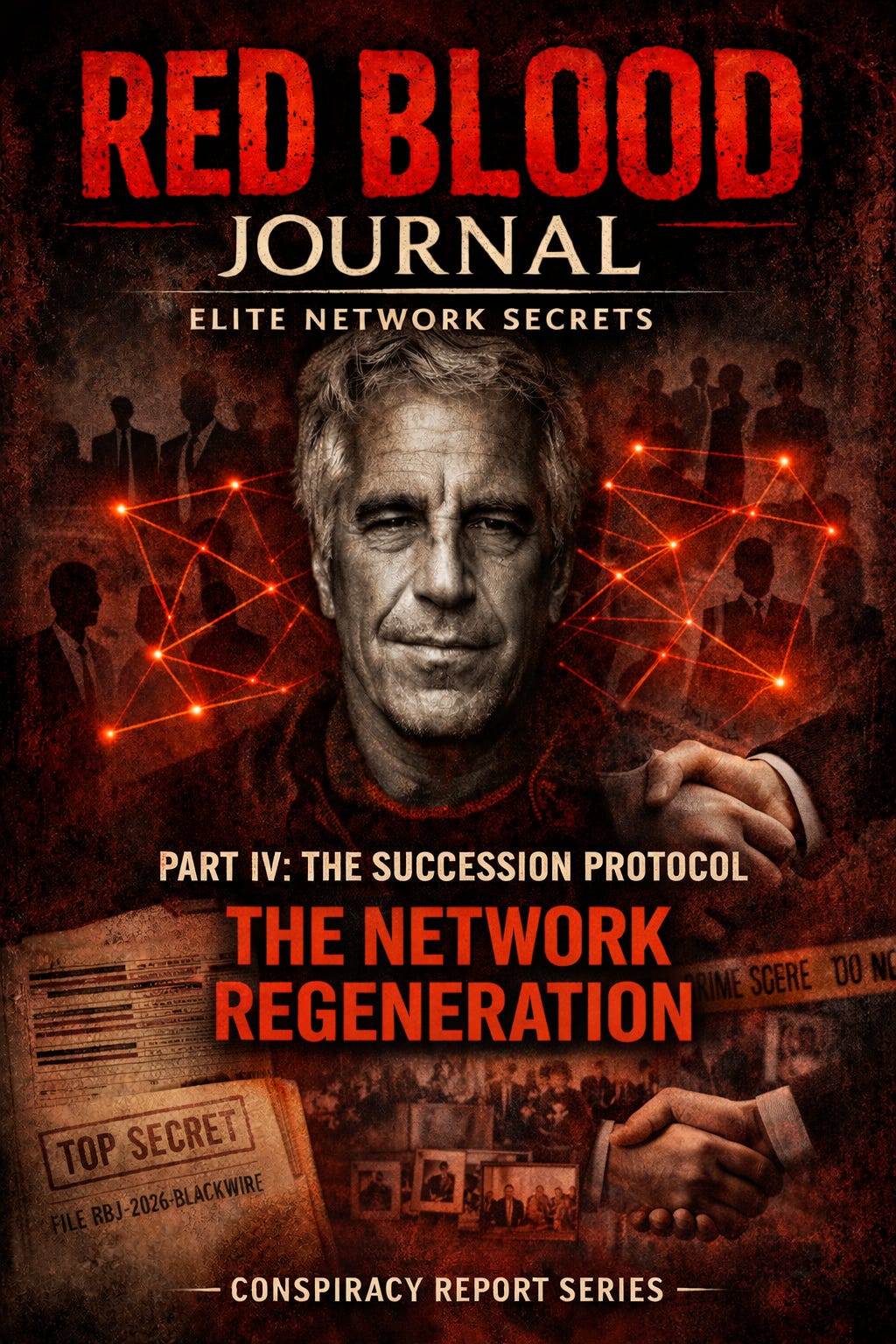
🩸 RED BLOOD JOURNAL TRANSMISSION
T#: RBJ-2026-BLACKWIRE-EPSTEIN-IV
Classification: Node Replacement Systems / Continuity of Influence Architecture / Succession and Regeneration Protocol
Desk: Counterintelligence Mythology Division — Archive of Blood & Signal
Volume: IV of V
Status: Successor Architecture Reconstruction Phase
PART IV — THE SUCCESSION PROTOCOL
PROLOGUE — NETWORKS DO NOT DIE. THEY MIGRATE.
When a man dies, his influence ends.
When a node disappears, the network reconfigures.
Jeffrey Epstein’s removal did not terminate the architecture that sustained him.
Because he was never the origin.
He was the visible interface.
Networks designed for influence are constructed with redundancy.
They anticipate exposure.
They anticipate removal.
They anticipate collapse.
And they prepare succession.
Not publicly.
Structurally.
SECTION I — THE REPLACEABLE NODE PRINCIPLE
Influence networks are built on modular design.
Each node performs a function.
Not a unique identity.
A function.
Access broker.
Information collector.
Social integrator.
Trust intermediary.
When one node is removed, another node emerges to fulfill the same function.
Not identical.
Compatible.
Because the network does not depend on the person.
It depends on the role.
SECTION II — THE SUCCESSION TRIGGER EVENT
Succession is not triggered by death.
It is triggered by exposure.
Exposure transforms an asset into a liability.
At that moment, preservation of the network requires separation from the exposed node.
Distance is created.
Public association dissolves.
Operational continuity shifts elsewhere.
This is not abandonment.
It is migration.
Migration ensures survival.
SECTION III — THE SHADOW PIPELINES
Epstein’s operational infrastructure did not consist solely of physical properties.
It consisted of relational pipelines.
Private introductions.
Social bridges.
Institutional gateways.
These pipelines do not disappear when a node disappears.
They persist in memory.
In contact networks.
In trust chains.
Trust is transferable.
Access is transferable.
Function is transferable.
The pipeline survives.
SECTION IV — THE LOW-VISIBILITY SUCCESSOR MODEL
The most effective successor does not replicate visibility.
Visibility invites scrutiny.
Scrutiny invites investigation.
Investigation invites exposure.
Therefore, succession often favors lower-visibility nodes.
Individuals already embedded in elite networks.
Individuals who do not attract public attention.
Individuals whose access appears natural.
Unremarkable.
Invisible.
Because invisibility is protection.
SECTION V — THE NETWORK IMMUNE RESPONSE
Exposure is treated as infection.
The network responds with containment.
Distance from the exposed node increases.
Communications shift.
Access routes reconfigure.
Public attention is redirected.
This is not coordination in the conscious sense.
It is structural adaptation.
Networks evolve.
The stronger the network, the faster the adaptation.
SECTION VI — THE DISTRIBUTION OF FUNCTION
The original node often performs multiple functions.
After removal, these functions disperse.
No single successor replaces the original node completely.
Instead, the functions fragment.
Access brokerage shifts to one node.
Social facilitation shifts to another.
Information preservation shifts elsewhere.
This fragmentation increases resilience.
Because it eliminates single points of failure.
SECTION VII — THE MOST LIKELY SUCCESSION OUTCOME
From the conspiracy analysis viewpoint, Epstein’s operational function did not disappear.
It redistributed.
His role as access facilitator likely fragmented across multiple individuals already positioned within elite social ecosystems.
His function as leverage archivist likely persisted within systems already designed to preserve information continuity.
His function as trust intermediary likely migrated to nodes whose legitimacy remained intact.
The network did not collapse.
It reorganized.
SECTION VIII — WHY SUCCESSION IS NECESSARY
Influence systems cannot tolerate structural voids.
Voids invite unpredictability.
Unpredictability threatens continuity.
Continuity is the primary objective.
Therefore succession is inevitable.
Not because individuals are irreplaceable.
Because functions are indispensable.
As long as power exists, influence mediation must exist.
As long as influence mediation exists, nodes will emerge to perform its function.
SECTION IX — THE INVISIBLE PRESENT
The successor node does not announce itself.
It operates quietly.
Without spectacle.
Without attention.
Because attention destroys function.
The most effective node is the one no one sees.
The one no one suspects.
The one that appears ordinary.
This is not concealment.
It is camouflage.
TERMINAL ASSESSMENT — VOLUME IV
From the conspiracy analysis perspective, Epstein’s removal represented a transition event, not a termination event.
His operational functions were redistributed across the existing network.
His role did not end.
It transformed.
Because networks built on influence cannot permit structural collapse.
They regenerate.
They adapt.
They survive.
Not through individuals.
Through architecture.
END TRANSMISSION — VOLUME IV
🕸️The Succession Protocol:
Network Regeneration Architecture
This text outlines a theory regarding power dynamics, suggesting that influential figures like Jeffrey Epstein function merely as expendable nodes within a larger, self-healing architecture.
When a high-profile individual is exposed or removed, the network does not collapse but instead undergoes a structural migration to ensure its survival.
According to this perspective, the functions of the removed person—such as access brokerage and information gathering—are redistributed among multiple, lower-profile successors to avoid future scrutiny.
This evolutionary process treats public scandal as a biological infection, triggering an immune response that fragments responsibilities to eliminate any single point of failure.
Ultimately, the source argues that these elite systems are designed for permanent continuity, prioritizing the preservation of the network’s influence over the fate of any specific member.
Successors remain effective by maintaining total invisibility, ensuring the underlying machinery of power operates without interruption or public detection.