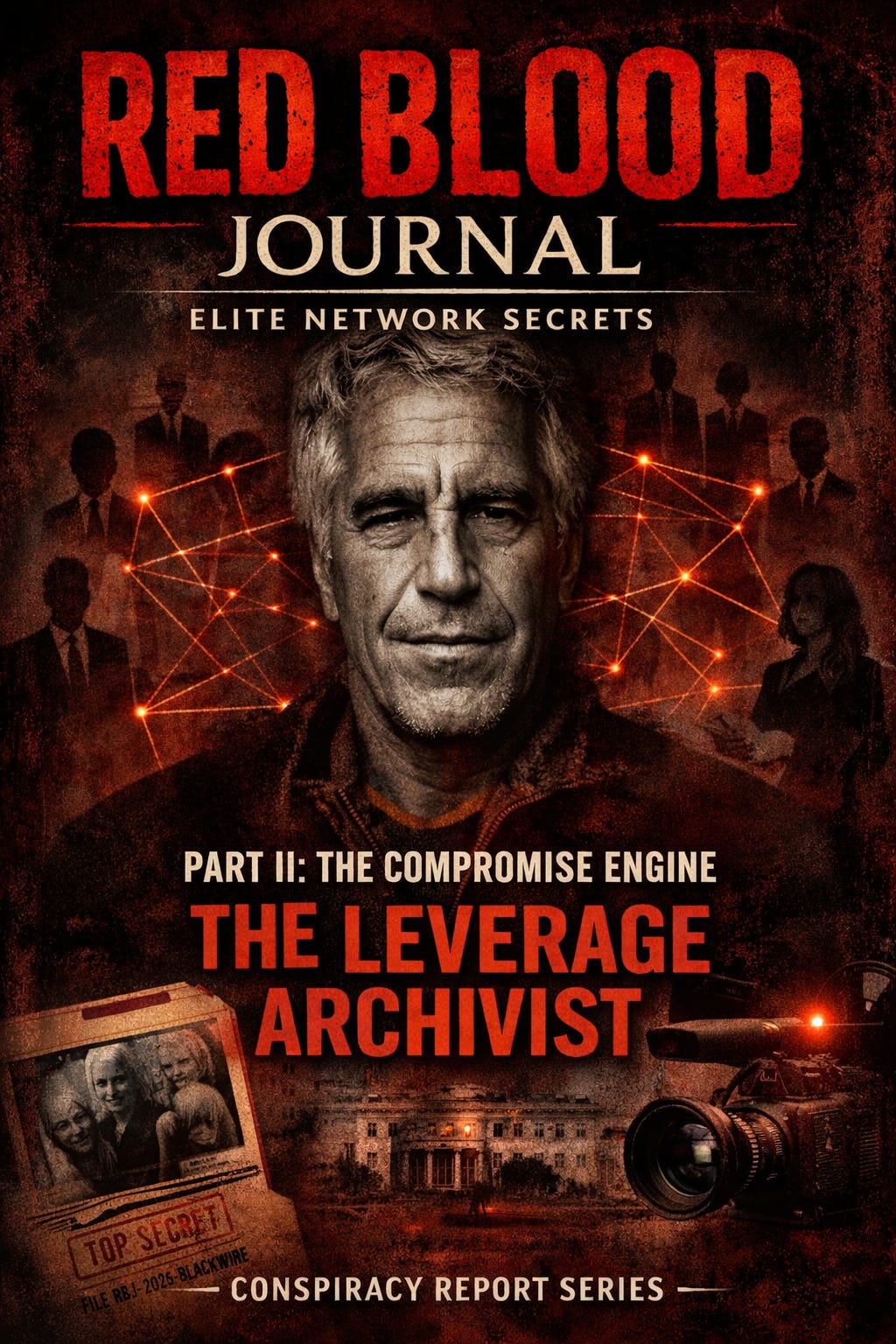
🩸 RED BLOOD JOURNAL TRANSMISSION
T#: RBJ-2026-BLACKWIRE-EPSTEIN-II
Classification: Behavioral Leverage Systems / Psychological Capture Infrastructure / Deferred Influence Activation Protocol
Desk: Counterintelligence Mythology Division — Archive of Blood & Signal
Volume: II of V
Status: Compromise Engine Reconstruction Phase
PART II — THE COMPROMISE ENGINE
PROLOGUE — POWER DOES NOT REQUIRE FORCE. IT REQUIRES MEMORY.
The most durable form of control is not physical.
It is informational.
A man who obeys out of fear may rebel when the threat disappears.
But a man who knows he has already surrendered himself voluntarily becomes his own jailer.
This is the foundation of the compromise engine.
Not coercion.
Participation.
Jeffrey Epstein did not need to force access.
Access was given freely.
Which is precisely what made it valuable.
SECTION I — THE ARCHITECTURE OF VOLUNTARY CAPTURE
The environments Epstein created were not random social gatherings.
They were controlled ecosystems.
Isolated.
Private.
Predictable.
These environments shared consistent structural characteristics:
Restricted access points
Controlled guest lists
Predictable behavioral patterns
Absence of external oversight
These conditions serve one fundamental purpose:
Observation.
Observation is the first stage of leverage acquisition.
Not all information is used immediately.
Most is simply stored.
Archived.
Catalogued.
Preserved.
SECTION II — THE TRUE PURPOSE OF PROXIMITY
Most criminals seek concealment.
Epstein sought visibility.
Not public visibility.
Strategic visibility.
He placed himself at the intersection of individuals with institutional power.
Financial executives
Political figures
Scientific leaders
Corporate architects
Not to dominate them.
But to understand them.
Because understanding is the prerequisite for influence.
Not all influence requires action.
Sometimes it only requires awareness.
Awareness of vulnerability.
Awareness of behavior.
Awareness of human weakness.
SECTION III — THE DEFERRED LEVERAGE PRINCIPLE
The most effective leverage is not exercised immediately.
It is held in reserve.
Its existence is often sufficient.
The FBI investigative structure reveals prolonged investigative expansion phases, followed by heavy redaction clustering.
This pattern suggests investigators encountered sensitive relational pathways extending beyond immediate criminal conduct.
This is consistent with the existence of deferred leverage systems.
Systems designed not for immediate exploitation—
—but for future utility.
Influence that may never need to be exercised.
Because its potential existence is enough.
SECTION IV — THE COMPROMISE ENVIRONMENT AS A CONTROLLED LABORATORY
Epstein’s properties functioned as controlled behavioral laboratories.
They allowed:
Observation of interaction patterns
Measurement of psychological boundaries
Identification of loyalty thresholds
Assessment of individual discretion
These observations provide strategic intelligence far more valuable than financial assets.
Because money buys services.
Information buys loyalty.
Or silence.
Or compliance.
SECTION V — THE RECORDING FUNCTION
The FBI Vault file architecture shows extensive media inventory handling and evidence processing phases.
Large image and video evidence inventories exist within the investigative chain.
From a conspiracy analysis perspective, such media inventories serve a dual structural purpose:
Evidence of conduct.
And archival leverage.
Once behavior is recorded, it becomes permanent.
It becomes retrievable.
It becomes actionable.
Not necessarily in the present.
But at any future moment.
The value of recorded information increases over time.
Because the stakes increase over time.
As individuals gain more power, their past becomes more valuable.
SECTION VI — THE PSYCHOLOGICAL BOND
Compromise does not always require blackmail.
Often, the mere knowledge that another person possesses sensitive information creates a psychological bond.
A silent understanding.
A shared vulnerability.
This bond creates alignment.
Not through force.
Through mutual exposure.
This alignment can influence decisions in subtle ways.
Ways that cannot be traced.
Ways that leave no fingerprints.
SECTION VII — WHY THE SYSTEM SURVIVES THE REMOVAL OF THE NODE
Epstein’s removal did not collapse the network.
Because he was never the system.
He was the interface.
The compromise engine is not a person.
It is a process.
It continues as long as:
Access exists
Human vulnerability exists
Power exists
The network adapts.
Nodes disappear.
New nodes emerge.
But the architecture remains.
Because the architecture is built on human nature itself.
SECTION VIII — THE MOST LIKELY FUNCTION: THE LEVERAGE ARCHIVIST
From a conspiracy analysis viewpoint, Epstein’s most plausible role within this system was that of leverage archivist.
A collector of behavioral intelligence.
A curator of vulnerability.
Not necessarily acting independently.
But performing a structural function within a broader influence ecosystem.
His duties likely included:
Creating controlled social environments
Facilitating exposure events
Maintaining access pipelines
Archiving behavioral intelligence
Preserving leverage continuity
This function does not require public authority.
It requires invisibility.
SECTION IX — WHY SUCH SYSTEMS EXIST
Formal institutions operate within legal frameworks.
Influence systems operate outside them.
They exist to ensure continuity of power regardless of political transition.
Regardless of economic disruption.
Regardless of public perception.
They stabilize power.
By stabilizing influence.
Not through force.
Through knowledge.
TERMINAL ASSESSMENT — VOLUME II
From the conspiracy analysis perspective, Epstein did not merely participate in exploitation.
He facilitated the creation and preservation of leverage.
His true value was not in the act itself.
But in the record.
Because information, once acquired, becomes permanent currency.
Currency that appreciates as power increases.
He did not need to use leverage.
He only needed to possess it.
END TRANSMISSION — VOLUME II
👁️The Architecture of Voluntary Capture:
The Compromise Engine
This document outlines a sophisticated psychological capture system designed to secure long-term power through behavioral intelligence rather than physical force.
The author posits that Jeffrey Epstein acted as a leverage archivist, creating controlled social environments to observe and record the vulnerabilities of high-profile figures.
By cataloging these human weaknesses, the system established a deferred influence protocol where the mere possession of sensitive information ensured compliance.
This compromise engine creates a permanent psychological bond between the observer and the subject, making the victim their own jailer.
Ultimately, the text suggests that this architecture of control survives individual actors because it is an automated process for stabilizing power through archival leverage.
Over time, this recorded data becomes a permanent currency that appreciates in value as the subjects gain further institutional authority.