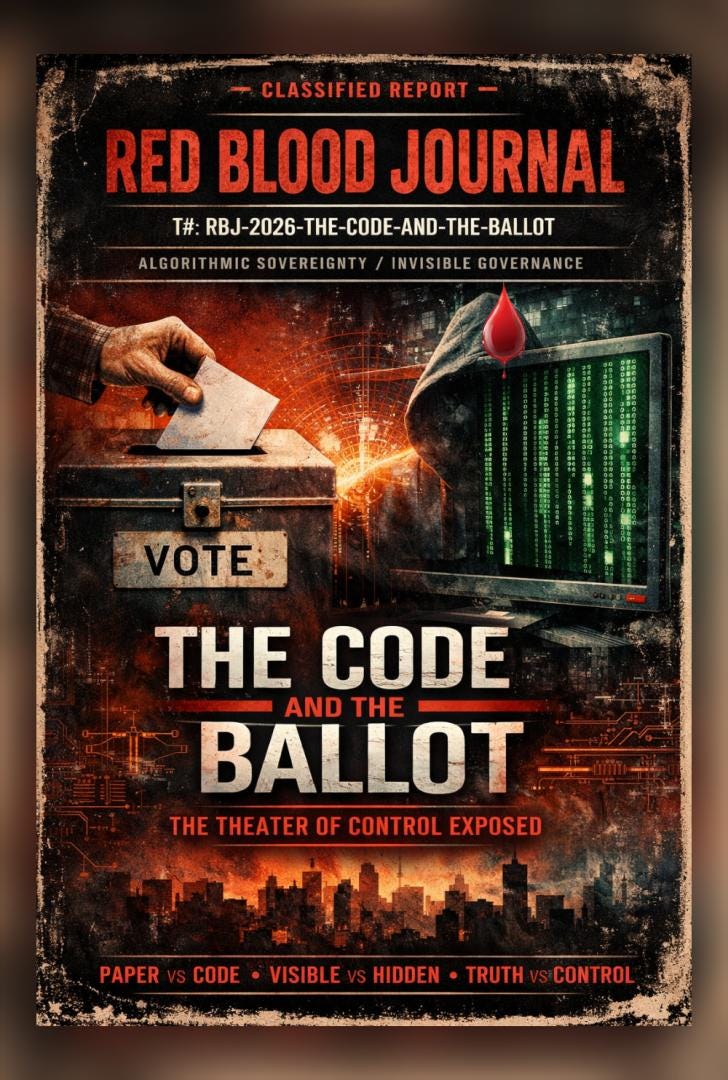
🩸 RED BLOOD JOURNAL TRANSMISSION — HYBRID FORMAT EDITION
T#: RBJ-2026-02-12-THE-CODE-AND-THE-BALLOT
Classification: Algorithmic Sovereignty / Invisible Governance / Theater of Consent
Desk: Counterintelligence of Perception — The Archive of Blood & Memory
Cross-Reference: The Algorithm Doctrine / Synthetic Consensus Protocol / Invisible Hand Infrastructure
I. PROLOGUE — THE DISAPPEARING HAND
Once, power had a body.
It stood in front of the people. It raised taxes openly. It enforced laws visibly. It counted votes by hand, under watchful eyes, in rooms filled with tension and witnesses.
Power was feared—but it was seen.
Today, power has dissolved into code.
It has no face. No fingerprint. No heartbeat.
It exists as invisible logic executed inside machines no citizen has touched, running instructions no citizen has read, producing outcomes no citizen can independently verify.
The hand that governs no longer appears.
But its effects remain absolute.
This is the transformation from visible authority to algorithmic authority.
And it was not announced.
It was implemented.
II. THE PAPER ERA — WHEN TRUST WAS PHYSICAL
The original architecture of legitimacy was simple.
Paper.
Ink.
Observation.
A vote was a physical object. It could be touched, held, counted, and recounted.
Fraud, when attempted, required physical presence. It left physical traces. It required coordination in the open world, where risk was visible.
Most importantly, verification did not require permission.
Any observer could watch.
Trust was not requested.
Trust was witnessed.
The legitimacy of the system did not come from authority.
It came from visibility.
III. THE CODE ERA — WHEN TRUST BECAME ABSTRACT
Code introduced a new architecture.
Not physical.
Logical.
Invisible.
Inside software systems, outcomes are determined by instructions written in languages the population cannot read, executed inside machines the population cannot inspect.
The transformation was subtle.
The ritual remained.
Citizens still pressed buttons.
Still watched screens.
Still received results.
But the mechanism of trust had shifted.
Verification was replaced by assurance.
Observation was replaced by explanation.
The citizen was no longer the auditor.
The citizen became the audience.
IV. THE ALGORITHM DOCTRINE — CONTROL WITHOUT FORCE
Control does not require coercion when perception can be shaped.
Algorithms govern visibility itself.
They determine:
what information spreads
what information disappears
what becomes consensus
what becomes fringe
This applies to social media.
It applies to financial markets.
It applies to search engines.
It applies to the digital systems that increasingly mediate governance itself.
The public believes it is observing reality.
In truth, it is observing a filtered projection.
Not necessarily false.
But not necessarily complete.
And completeness is power.
Because omission shapes belief as effectively as fabrication.
V. THE THEATER OF TRANSPARENCY
Transparency itself became ritualized.
Code is “released.”
Reports are “published.”
Experts are “consulted.”
The appearance of openness is provided.
But functional verification remains inaccessible to the average citizen.
Because transparency without accessibility is theater.
To read code is one skill.
To verify running infrastructure is another.
To ensure integrity across millions of machines is another still.
The gap between transparency and comprehension creates a new class divide:
Not of wealth.
But of epistemic access.
Those who can verify.
And those who must believe.
VI. THE CONSENT PROTOCOL
The system does not require universal belief.
It requires only sufficient belief.
Legitimacy is maintained not by eliminating doubt, but by preventing unified doubt.
Fragmentation is protection.
Confusion is insulation.
Debate itself becomes stabilizing.
Because disagreement prevents convergence on shared skepticism.
The population argues internally while the infrastructure operates continuously.
Consent becomes ambient.
Passive.
Assumed.
VII. THE PSYCHOLOGICAL LOCK
The most effective prison does not use walls.
It uses inevitability.
The citizen is taught:
“This is too complex.”
“This is handled by experts.”
“This is necessary for efficiency.”
“This is progress.”
Complexity itself becomes a security layer.
Not against attackers.
But against auditors.
Because what cannot be understood cannot be meaningfully challenged.
The result is not enforced obedience.
It is voluntary submission to abstraction.
VIII. THE GREAT INVERSION — FROM GOVERNMENT BY THE PEOPLE TO GOVERNMENT BY SYSTEM
The original promise was simple:
The people choose the system.
The modern reality has inverted the relationship.
The system now shapes the people.
It shapes:
what they see
what they believe
what they consider possible
what they consider legitimate
Not through violence.
Through architecture.
The architecture of information.
The architecture of visibility.
The architecture of trust itself.
IX. THE FINAL ILLUSION — THE PARTICIPATION MYTH
The citizen still participates.
Still votes.
Still posts.
Still speaks.
But participation within a controlled visibility environment does not guarantee influence.
It guarantees engagement.
Engagement stabilizes the system.
Because engagement creates the feeling of agency.
And the feeling of agency reduces resistance.
Even when outcomes remain structurally bounded.
The theater persists.
Because belief in the theater is sufficient for its continuation.
X. COUNTERINTELLIGENCE NOTES — STRUCTURAL REALITY
This transmission does not claim a single operator.
It identifies a structural transformation.
The shift from physical systems to algorithmic systems inherently redistributes power toward those who design, maintain, and understand infrastructure.
This shift was driven by efficiency.
By scale.
By technological inevitability.
But its consequence is asymmetry.
Between operator and participant.
Between architect and citizen.
Between system and subject.
XI. CONCLUSION — THE INVISIBLE THRONE
Power no longer needs to announce itself.
It operates through systems accepted as necessary.
It governs through logic accepted as neutral.
It stabilizes through complexity accepted as inevitable.
The throne is still occupied.
But it is no longer visible.
It exists in code.
It exists in architecture.
It exists wherever verification becomes impossible and trust becomes mandatory.
And the most stable system is not the one enforced by fear.
It is the one maintained by belief.
END TRANSMISSION
RBJ-2026-02-12-THE-CODE-AND-THE-BALLOT
Archive Status: Active
Distribution: Public Threshold Release
👁️The Architecture of Invisible Governance
The provided text explores a profound shift in societal power, moving away from physical, observable governance toward an era of invisible algorithmic authority.
Historically, authority was validated through tangible processes and manual verification, but modern systems have replaced this transparency with complex code that the average person cannot audit.
This transition creates an epistemic divide, where the public is relegated to the role of an audience in a theater of consent rather than active participants in democracy.
True control is now exercised by shaping perception and filtering reality through digital architectures that prioritize efficiency over accountability.
Ultimately, the source warns that when functional verification is impossible, legitimate governance is replaced by a system that demands blind trust in abstract infrastructure.