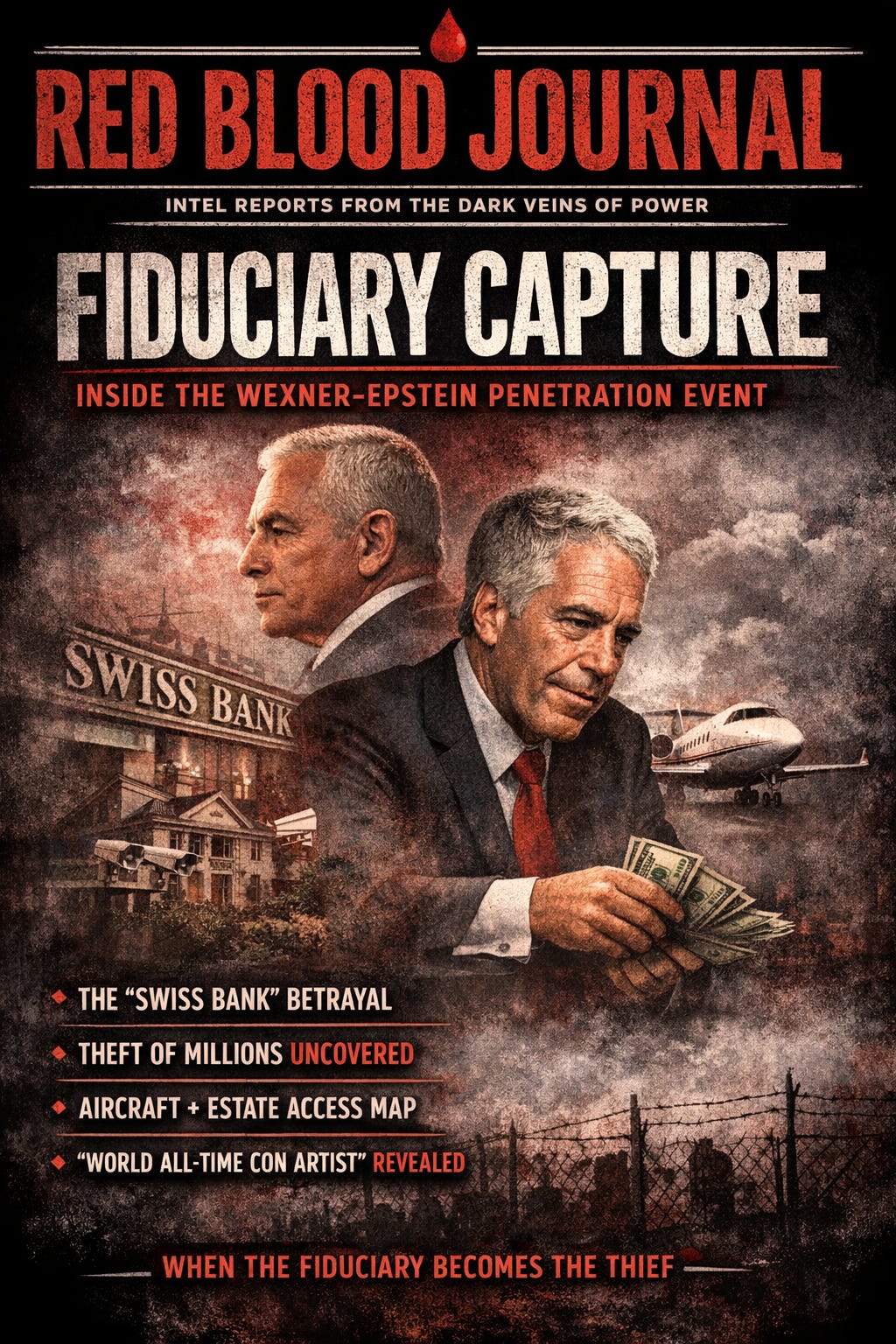
🩸 RED BLOOD JOURNAL TRANSMISSION
T#: RBJ-2026-FIDUCIARY-VEIL
Classification: Access Architecture / Fiduciary Penetration Event / Control Surface Exposure
Desk: Counterintelligence Analysis Wing — Archive of Blood & Memory
Source Base: House Oversight Committee Deposition of Leslie H. Wexner (2026)
PROLOGUE — ACCESS IS POWER
Power rarely appears as force.
It appears as access.
Not access to buildings.
Not access to planes.
Not access to social circles.
Access to trust infrastructure.
The deposition of Leslie Wexner reveals not merely a relationship between a wealthy principal and an advisor—but the anatomy of a penetration event.
Not necessarily penetration of physical space.
Penetration of governance itself.
Because when fiduciary access is granted, the perimeter moves inward.
And when the perimeter moves inward, the system becomes indistinguishable from the operator.
SECTION I — THE FIDUCIARY VEIL
The most important admission appears almost casually:
“He was kind of the business manager of my personal affairs.”
Les Wexner Testiony About Epste…
This single sentence collapses the defensive perimeter.
Because “personal affairs” is not a narrow domain.
It is the nexus point of:
Financial routing
Asset control
Legal authorization
Transaction visibility
Signature authority
A fiduciary does not merely advise.
A fiduciary acts.
And action is the most dangerous form of access.
Wexner further explains Epstein became trustee partly as a “convenience for signing documents.”
Les Wexner Testiony About Epste…
Convenience.
The most lethal word in security architecture.
Because convenience bypasses scrutiny.
Convenience removes friction.
Convenience replaces verification with assumption.
SECTION II — THE SWISS BANK SIGNAL
One of the most revealing structural indicators emerges in Wexner’s description of Epstein’s communications:
Epstein would call urgently.
He would say he was “in Switzerland talking to a Swiss bank.”
He would frame the transaction as complex.
He would explain that Wexner “wouldn’t understand.”
Les Wexner Testiony About Epste…
Then the most critical admission appears:
“He was probably in bed in New York… I didn’t know where the hell he was.”
Les Wexner Testiony About Epste…
This is not merely uncertainty.
It is loss of verification.
Loss of verification is loss of control.
When an operator can claim international financial activity while their physical location is unknown, the principal is no longer directing the system.
The system is directing itself.
SECTION III — THE THEFT EVENT
The fracture becomes visible when Wexner’s wife assumes control of financial oversight.
Discovery follows.
Epstein “had stole money from us.”
Les Wexner Testiony About Epste…
This admission reveals the logical conclusion of unchecked fiduciary penetration.
Access precedes theft.
Authority precedes extraction.
But the deposition contains a deeper silence.
No amount is specified.
No mechanism described.
No pathway mapped.
No structural explanation provided.
Only the conclusion.
The presence of theft without structural analysis leaves the most important question unresolved:
How did the architecture permit it?
SECTION IV — THE AIRCRAFT PARADOX
The aircraft becomes a symbolic object within the testimony.
At first, Epstein “very rarely” flew on the plane.
Les Wexner Testiony About Epste…
Then, Wexner says he does not believe he ever provided flights.
Then:
Epstein was on the plane.
Then:
After conferring with counsel, Wexner clarifies he remembers Epstein being on a plane, but not necessarily at the destination event.
Les Wexner Testiony About Epste…
This sequence reveals something subtle but critical.
Access existed.
Memory attempts to narrow it.
But access leaves structural evidence even when memory retreats.
Aircraft access represents more than transportation.
It represents network access.
Entry into the physical pathways of elite infrastructure.
SECTION V — THE ESTATE WITHOUT VISIBILITY
Wexner confirms:
Approximately 20 staff operated on the property.
Private security existed since 1975.
Les Wexner Testiony About Epste…
Yet when confronted with allegations that Epstein survivor Maria Farmer stayed on property connected to his estate, Wexner states:
He knew her name only from press.
He did not know whether she stayed there.
Les Wexner Testiony About Epste…
This is not contradiction.
It is compartmentalization.
Large estates operate like micro-states.
Principals do not observe every movement.
They observe through systems.
If the system is penetrated, visibility dissolves.
SECTION VI — THE TRUST BREACH TIMELINE
The deposition outlines a sequence consistent with structural infiltration patterns:
Phase 1 — Introduction
Epstein enters as advisor.
Phase 2 — Expansion
Epstein gains fiduciary and trustee authority.
Phase 3 — Operational Autonomy
Epstein conducts financial communications independently.
Phase 4 — Verification Collapse
Principal cannot verify location or actions.
Phase 5 — Extraction Event
Financial theft discovered.
Phase 6 — Severance
Relationship terminated once breach becomes undeniable.
This pattern is consistent across infiltration events in financial systems.
Authority granted.
Verification relaxed.
Control transferred.
Extraction follows.
SECTION VII — THE CON ARTIST STATEMENT
Perhaps the most revealing psychological admission occurs when Wexner describes Epstein:
“I was conned by the World Olympic all-time con artist.”
Les Wexner Testiony About Epste…
This statement reframes the relationship entirely.
Not as collaboration.
Not as partnership.
But as asymmetric control.
The operator understood the system.
The principal did not.
SECTION VIII — THE CONTROL SURFACE MODEL
From the deposition alone, Epstein gained confirmed access to:
Financial authority surfaces
Trustee and fiduciary roles
Communication authority surfaces
Direct banking interactions
Physical authority surfaces
Estate proximity and aircraft access
Administrative authority surfaces
Inventory and financial management functions
Each access surface increases operational freedom.
Combined, they form a complete access architecture.
FINAL ASSESSMENT — THE FIDUCIARY PENETRATION EVENT
The deposition does not prove intent beyond theft.
It does not claim coordination beyond advisory roles.
It does not establish foreknowledge beyond belief in denial.
But it reveals something structurally undeniable:
Jeffrey Epstein was granted fiduciary access inside the trust infrastructure of one of the most powerful private financial ecosystems in the world.
He operated within that infrastructure.
He acted independently within it.
He extracted from it.
And only after extraction was control reasserted.
ARCHIVE NOTE
The most dangerous penetration is not forced entry.
It is invited entry.
Because forced entry triggers alarms.
Invited entry disables them.
End Transmission
🪱Architecture of the Invited Breach:
The Fiduciary Penetration Event
This document analyzes the structural infiltration of Leslie Wexner’s private financial empire by Jeffrey Epstein, utilizing deposition testimony to map a fiduciary penetration event.
By securing roles as a trustee and business manager, Epstein gained unfettered access to legal and financial systems under the guise of professional convenience.
This authority allowed him to bypass traditional security protocols, eventually leading to the discovery of significant monetary theft.
The text emphasizes that invited entry is the most lethal form of security breach because it effectively disables internal oversight.
Ultimately, the narrative illustrates how compartmentalized governance and a lack of verification allowed an operator to exert asymmetric control over a powerful principal’s assets.
Epstein’s ability to manipulate elite infrastructure highlights a total collapse of defensive perimeters within a high-stakes financial ecosystem.