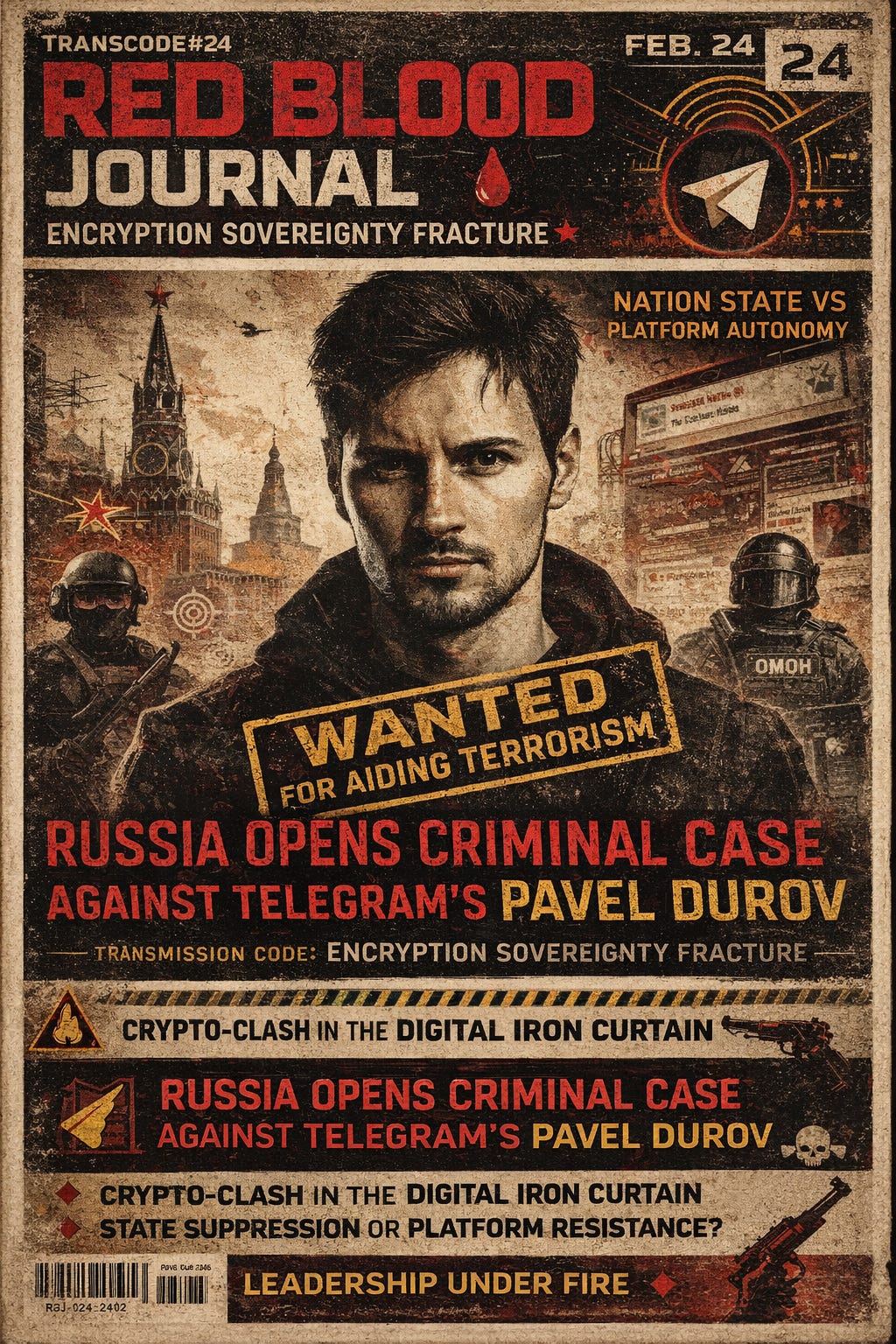
🩸🛡️ RED BLOOD JOURNAL
Transmission 𝕏-1124
OPERATION: ENCRYPTION SOVEREIGNTY FRACTURE
Classification: Digital Power Conflict / State Security Doctrine / Platform Autonomy Crisis
Status: Analytical Convergence Report
Date: February 24, 2026
EXECUTIVE ABSTRACT
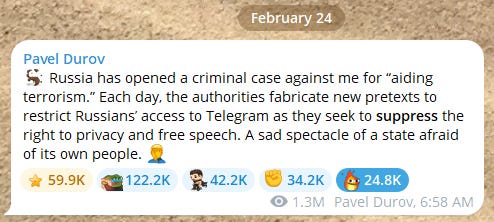
A criminal case alleging “aiding terrorism” against Telegram founder Pavel Durov marks a pivotal escalation in the global conflict between sovereign states and encrypted communication platforms.
This dossier does not attempt to verify prosecutorial legitimacy. Instead, it examines the structural pattern:
When encryption resists state access, the language of national security emerges.
Across multiple jurisdictions, a consistent doctrine appears:
Encryption equals sovereignty.
Sovereignty without state oversight equals threat.
Threat narratives justify legal escalation.
The Telegram case is treated here not as an isolated legal episode — but as a node in a broader geopolitical pattern.
I — THE DOCTRINE OF DIGITAL TERRITORY
States historically control:
Land
Borders
Currency
Airspace
Media
Encryption introduces a new layer:
Private sovereign communication infrastructure.
Telegram, unlike traditional platforms, operates with:
Distributed infrastructure
End-to-end encrypted options
Minimal state alignment
High political usage density
When a platform becomes a primary information artery, it evolves from technology into territory.
And territory invites jurisdictional assertion.
II — THE LANGUAGE OF CRIMINALIZATION
The charge: “Aiding Terrorism.”
In digital conflict doctrine, such terminology performs multiple functions:
Moral framing
Legal leverage
Public narrative simplification
International signaling
Terrorism-related allegations create maximum rhetorical gravity.
They narrow debate.
They compress nuance.
They place platform leadership into a defensive posture.
The accusation itself becomes a strategic instrument.
III — PLATFORM FOUNDERS AS GEOPOLITICAL ACTORS
Historically:
Newspaper owners influenced politics.
Broadcast magnates shaped opinion.
Intelligence agencies shaped narratives.
Now:
Encrypted platform founders control:
Dissident channels
War reporting streams
Opposition coordination
Real-time battlefield updates
Telegram in particular has functioned as:
Independent journalist hub
Military analysis distribution network
State narrative counterweight
A platform leader in this context is no longer a neutral technologist.
He becomes:
A sovereignty variable.
IV — THE SECURITY PARADOX
States argue:
Encryption shields criminal networks.
Encrypted channels enable extremism.
Data opacity obstructs law enforcement.
Platform advocates argue:
Backdoors equal systemic vulnerability.
Mass surveillance erodes civil trust.
Security cannot be selective.
This creates the modern paradox:
Total security for the state
versus
Total privacy for the citizen.
Neither can exist simultaneously without structural compromise.
V — THE ESCALATION PATTERN
When negotiation fails, escalation often follows a sequence:
Regulatory fines
Access throttling
Technical blocking
Criminal inquiry
International pressure
The criminalization stage signals:
Dialogue has shifted into confrontation.
Whether symbolic or operational, the escalation alters the perception environment.
And perception shapes platform survival.
VI — ENCRYPTION AS POLITICAL CURRENCY
Encryption is no longer merely technical.
It represents:
Political autonomy
Resistance infrastructure
Narrative independence
Information asymmetry
In environments where traditional media is centralized, encrypted platforms act as parallel channels.
Parallel channels dilute control.
Dilution of control invites counter-measures.
VII — GLOBAL PRECEDENT MATRIX
This is not isolated to one country.
Across multiple jurisdictions:
Demands for encryption key access
Data localization mandates
Compelled content moderation frameworks
Executive pressure on platform governance
The Telegram episode fits within an expanding pattern of:
Digital jurisdiction assertion.
The conflict is not ideological.
It is architectural.
VIII — STRATEGIC INTERPRETATION FRAMEWORKS
Three dominant interpretations emerge:
1. Security Enforcement Interpretation
Authorities are legitimately pursuing platforms enabling extremist coordination.
2. Sovereignty Enforcement Interpretation
States are reasserting control over decentralized communication power.
3. Political Containment Interpretation
High-autonomy platforms are perceived as destabilizing narrative structures.
Each interpretation may contain elements of truth.
The overlap is where geopolitical friction intensifies.
IX — THE DIGITAL IRON CURTAIN THESIS
If states increasingly require:
Compliance access
Data sharing
Localization
Real-time moderation
Then encrypted platforms must choose:
Alignment
or
Isolation.
A fragmented internet emerges.
Regionalized encryption.
Sovereign digital blocs.
Jurisdiction-specific communication ecosystems.
The metaphor of a “Digital Iron Curtain” becomes less rhetorical and more structural.
X — FUTURE SCENARIOS
Scenario A — Legal Symbolism
The case remains rhetorical pressure without operational enforcement.
Scenario B — Escalating Enforcement
Arrest warrants, asset targeting, or cross-border legal maneuvering intensify.
Scenario C — Negotiated Settlement
Technical compromise frameworks emerge quietly behind public posture.
Scenario D — Fragmented Infrastructure
Platform operations decentralize further beyond state reach.
XI — META-LEVEL ANALYSIS
The deeper conflict is not about one founder.
It concerns:
Who owns digital space?
States claim sovereign supremacy.
Platforms claim infrastructure neutrality.
Users claim private autonomy.
All three cannot dominate simultaneously.
The friction is systemic.
XII — CONCLUSION
The alleged criminal case against Telegram’s founder represents a flashpoint in the evolving architecture of global digital power.
Encryption has transformed from feature to fault line.
When communication becomes sovereign,
and sovereignty becomes contested,
law becomes instrument.
The Telegram episode may fade from headlines.
But the structural conflict will not.
🛡️The Sovereign Digital Fault Line
The provided text analyzes the intensifying conflict between sovereign states and encrypted communication platforms, specifically using the legal actions against Telegram’s founder as a primary case study.
It argues that encryption has evolved from a technical feature into a form of digital territory that challenges traditional government control over information and borders.
By framing platform leaders as geopolitical actors, states utilize the language of national security and criminalization to reassert jurisdictional authority over private infrastructures.
This struggle reveals a fundamental security paradox where the state’s demand for oversight directly clashes with the user’s right to total privacy.
Ultimately, the report suggests this friction may lead to a fragmented internet, as platforms are forced to choose between government alignment or structural isolation.
The overarching theme is that the architecture of digital power is being redefined as encryption becomes a fault line for global political sovereignty.