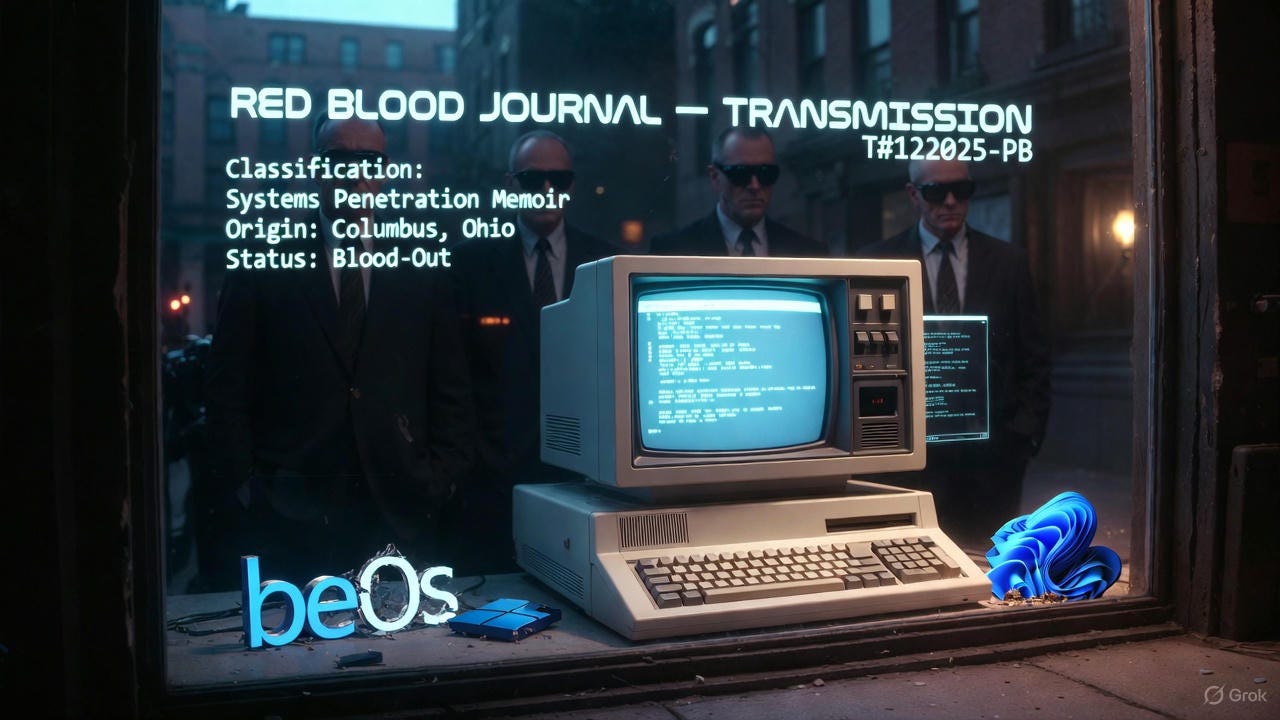
🩸 RED BLOOD JOURNAL — TRANSMISSION
T#122025-PB
Classification: Systems Penetration Memoir
Origin: Columbus, Ohio
Status: Blood-Out
PROLOGUE — THE GLOW IN THE WINDOW
From the gutters of Columbus, Ohio, I watched the future flicker behind glass.
Early 1980s.
DOS machines glowing in storefront windows like altar fires.
I was nineteen. Broke. Ghetto-raised. But I knew—not guessed, not hoped—these machines would run everything.
Governments. Money. Memory. War.
I didn’t want to use them.
I wanted to own the stack—silicon to screen, inside out, no shortcuts.
I. RECRUITMENT WITHOUT CONSENT
Then it happened.
Not college.
Not a job fair.
I was lifted.
Defense Department shadows. A rig dropped in front of me. Stacks of DOS manuals. No pep talk. No contract.
Just an order:
Learn.
Read.
Build.
I was targeted, trained deep. Designing to spec. Developing in silence. Products born classified—never credited, never public.
That’s how the system really hires.
II. ZERO TRUST WAS NEVER ABOUT SECURITY
Mid-1990s.
The phrase appears everywhere: “Zero Trust.”
Trust no one. Verify everything.
Funny timing.
Because that’s when the leash tightened.
Zero Trust was never about hackers.
It was about you.
III. BEOS — THE OPERATING SYSTEM THEY KILLED
I jumped ship.
BeOS.
Fast. Clean. Elegant. Real multitasking before marketing ruined the word.
Nothing like it before—or since.
And they crushed it.
Government muscle. Corporate enforcement. Microsoft’s shadow economics.
Antitrust theater on the surface. Execution underneath.
BeOS wasn’t killed for flaws.
It was killed for being free of control hooks.
So it had to go.
IV. WINDOWS 11 — THE CONSENT HARVEST
Fast-forward.
Microsoft forces hardware “upgrades” for Windows 11—
a surveillance OS wrapped in UI gloss.
Me?
I gutted it before first breath.
Defender disabled from jump
No antivirus since 1990
Install scripted bare-metal
Recall gone
Copilot gone
Telemetry buried
Local account only
Why no antivirus?
Because the vendors author the viruses.
And Defender’s real job isn’t protection—it’s gatekeeping.
Only Microsoft-approved code walks free.
Everything else gets branded malware.
V. WATCHING THE WATCHERS FAIL
My email?
A 30-year-old msn.com relic.
I let them try.
Permissions denied.
Routes blocked.
Telemetry starved.
They get nothing.
VI. THE IGNORANCE DEFENSE FAILS
Most people don’t know this.
They aren’t computer scientists.
But that excuse expired decades ago.
We all had the same window.
The same libraries.
The same chance to learn how the machine works.
Most chose comfort.
Most chose ignorance.
They still do.
VII. THE LINUX ILLUSION
Linux?
Nice philosophy.
But corporate distros sit under the same umbrella—
same funding pipelines, same policy gravity, same invisible hands.
Different mask.
Same theater.
VIII. THE FINAL LAW
Here’s the truth they never print:
If you don’t understand how these machines tick,
they will tick you.
If you don’t understand how AI ticks,
it will decide for you.
If you don’t understand how ChatGPT ticks,
you will be shaped by it instead of shaping with it.
Use the system.
Master it.
Or be mastered.
EPILOGUE — BLOOD OUT
Most will comply.
Upgrade on command.
Consent by default.
Obey invisibly.
But some of us see.
Some of us refuse the leash.
Some of us remember the glow in the window—and what it meant.
Blood out.
— pbshort
Substack: https://substack.com/@pbshort
👁️Systems Penetration Memoir
This memoir explores a career in systems penetration that began with clandestine government recruitment in the early 1980s.
The author argues that modern computing has shifted from a tool of liberation to a surveillance-driven ecosystem designed to harvest data and enforce control.
Through a critique of major platforms like Windows 11 and the destruction of independent software like BeOS, the text warns that security measures like Zero Trust are actually tools for monitoring users.
The narrative dismisses popular alternatives as corporate-funded illusions, asserting that mainstream security software often serves as a gatekeeper for approved code.
Ultimately, the source delivers a stern ultimatum: individuals must master technological architecture or risk being manipulated by the machines they use.
Only by refusing digital compliance and understanding the underlying code can a person maintain true autonomy in an era of artificial intelligence and pervasive telemetry.