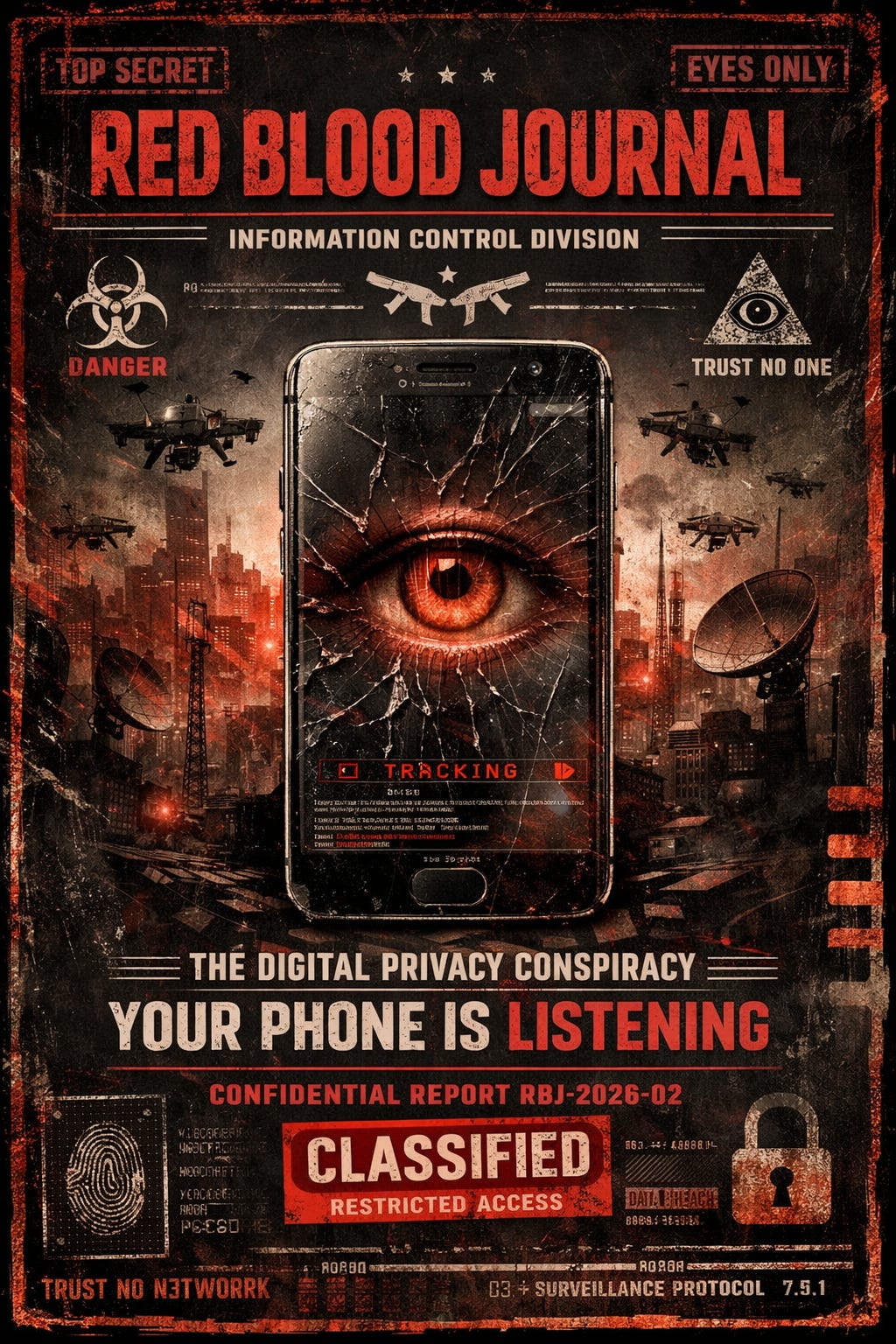
🩸 RED BLOOD JOURNAL TRANSMISSION — DIGITAL CONTROL EDITION
T#: RBJ-2026-02-DIGITAL-PRIVACY-LISTENING-DEVICE
Classification: Strategic Surveillance / Behavioral Extraction / Device-Level Control Architecture
Desk: Cryptographic Resistance Division
Source: Technical interview with privacy expert and cryptography founder
Digital Privacy Expert Explains…
PROLOGUE — THE DEVICE IN YOUR HAND IS NOT WHAT YOU THINK
There was a time when a phone was just a phone.
It rang.
It transmitted sound.
It stayed silent when placed face-down.
Today, it watches.
It listens.
It records behavior—not always in the obvious sense of “audio recording,” but in something far more powerful:
Prediction.
Prediction is control.
The attached interview reveals a truth hidden beneath the glossy surface of modern technology:
The real purpose of many digital systems is not to serve the user.
It is to extract the user.
Modern digital platforms extract value by collecting behavior data, recording interactions, and using it to predict and influence future behavior.
Digital Privacy Expert Explains…
This is not science fiction.
This is the operating model.
SECTION I — YOUR PHONE IS A SURVEILLANCE SENSOR, NOT JUST A TOOL
Every action performed on a smartphone creates data.
Not just messages.
Not just calls.
Everything:
• Location
• Movement patterns
• Typing rhythm
• Contacts
• Search history
• App usage
• Device identifiers
• Microphone triggers
• Camera access events
These signals form a complete behavioral fingerprint.
Companies collect this information because it allows them to predict decisions.
And prediction allows influence.
Every bit of information collected from behavior allows companies to predict and steer actions.
Digital Privacy Expert Explains…
This is called:
Surveillance Capitalism.
It is the economic model of the digital age.
You are not the customer.
You are the resource.
SECTION II — YOUR PHONE DOES NOT NEED TO “LISTEN” CONSTANTLY TO KNOW EVERYTHING
This is the critical misunderstanding most people have.
The phone does not need to record your conversations 24/7 to know what you are thinking.
It only needs enough data points to build a behavioral model.
Example:
If you:
• Search for hiking boots
• Walk near outdoor stores
• Talk to hikers
• Spend time on hiking websites
• Visit hiking locations
The system predicts you will buy hiking gear.
It does not need your private conversations.
Your behavior already revealed everything.
This is more efficient than listening.
Because behavior does not lie.
SECTION III — THE REAL WEAKNESS IS NOT ENCRYPTION — IT IS THE DEVICE ITSELF
Encryption works.
Mathematically, encryption is extremely strong.
It is nearly impossible to break without the key.
Encryption allows secrets to be created that even powerful supercomputers cannot recover without permission.
Digital Privacy Expert Explains…
But there is a fatal weakness.
Not the message.
The phone.
Because the phone must decrypt messages to show them to you.
Which means:
If someone controls your phone…
They control everything.
If an attacker gains access to your phone itself, encryption no longer protects you because they control the device that decrypts the information.
Digital Privacy Expert Explains…
Encryption protects transmission.
It does not protect compromised hardware.
This distinction is critical.
SECTION IV — THERE ARE TWO LEVELS OF SURVEILLANCE
Tactical Surveillance — Targeting Individuals
This is when a specific person is monitored.
Examples:
• Journalists
• Political figures
• Activists
• High-value targets
This requires effort and resources.
It is selective.
Strategic Surveillance — Monitoring Everyone
This is the modern model.
Collect everything.
Store everything.
Use later if needed.
Strategic surveillance involves collecting and storing data on everyone, even without immediate need, for future use.
Digital Privacy Expert Explains…
This is more efficient.
Because it creates a permanent historical record of human behavior.
A digital memory system.
SECTION V — YOUR PHONE CAN BE COMPROMISED WITHOUT YOU KNOWING
This is not theoretical.
It has already happened.
Example described in the source:
A malicious image message could automatically download.
The image contains hidden code.
Once downloaded, it executes silently.
The attacker gains full control of the phone.
Malicious messages exploiting software flaws have allowed attackers to gain full access to phones without user interaction.
Digital Privacy Expert Explains…
No clicking required.
No warning.
No visible sign.
From that moment forward:
The attacker sees everything.
SECTION VI — EVEN GOVERNMENTS HAVE ATTEMPTED TO WEAKEN ENCRYPTION
One of the most disturbing revelations in the source involves cryptographic backdoors.
Government agencies attempted to introduce fake “randomness” into encryption standards.
This allowed them to secretly decrypt communications.
The NSA promoted encryption standards later revealed to contain weaknesses that allowed decryption by those with secret knowledge.
Digital Privacy Expert Explains…
This program was exposed by Edward Snowden.
This proves something critical:
Control over encryption equals control over privacy.
Control over privacy equals control over individuals.
SECTION VII — THE REAL PURPOSE IS BEHAVIORAL CONTROL, NOT JUST SURVEILLANCE
Surveillance is not the end goal.
Prediction is.
Prediction allows influence.
Influence allows control.
If a system knows:
• What you believe
• What you fear
• What you want
• What you will do
It can shape your environment to guide your decisions.
Without force.
Without violence.
Without you realizing.
SECTION VIII — WHY FREE APPS ARE NEVER REALLY FREE
The question everyone should ask:
Why are trillion-dollar companies giving away services for free?
Because the product is not the app.
The product is you.
Your behavior is the resource.
Your attention is the commodity.
Your psychology is the target.
SECTION IX — CAN YOU STOP YOUR PHONE FROM LISTENING?
Yes.
But not completely.
Because the system is larger than any single setting.
However, risk can be reduced significantly.
The privacy expert described the most secure method:
Use a dedicated phone only for secure communication.
No extra apps.
No browsing.
No social media.
Using a dedicated phone with only secure encrypted messaging significantly reduces surveillance risk.
Digital Privacy Expert Explains…
Because complexity creates vulnerabilities.
Simplicity creates security.
SECTION X — THE TRUE CONSPIRACY IS NOT THAT YOUR PHONE LISTENS
The real truth is more subtle.
More disturbing.
Your phone does not need to listen constantly.
Because it already knows you.
Through:
Patterns.
Habits.
Behavior.
Prediction.
The system does not need your words.
It has your digital shadow.
And your digital shadow reveals everything.
FINAL ASSESSMENT — THE DEVICE IS THE INTERFACE BETWEEN HUMAN AND SYSTEM
Your phone is not just a tool.
It is an interface.
Between you and the digital infrastructure.
Between your thoughts and the algorithm.
Between human freedom and machine prediction.
Encryption protects messages.
But control of devices protects power.
And power always seeks visibility.
Because visibility enables control.
COUNTERMEASURES — PLAIN ENGLISH SUMMARY FOR EVERYONE
If someone wants to protect privacy, these steps matter most:
• Disable unnecessary app permissions
• Turn off microphone access for most apps
• Avoid installing unknown apps
• Use encrypted messaging apps like Signal
• Keep software updated
• Avoid clicking unknown links
• Use a separate phone for sensitive communication
Most importantly:
Understand the system.
Because awareness is the first form of resistance.
👁️The Digital Shadow:
Surveillance Architecture and Behavioral Control
This text explores the concept of surveillance capitalism, where smartphones serve as sophisticated tracking sensors rather than simple tools.
It argues that modern technology focuses on extracting behavioral data to predict and influence user decisions, rendering traditional microphone “listening” unnecessary.
While mathematical encryption remains strong, the source highlights that the physical device is the primary point of failure if compromised by malicious software or government backdoors.
The narrative emphasizes that strategic surveillance transforms individuals into resources, turning their digital habits into a permanent historical record.
Ultimately, the expert suggests that achieving true privacy requires reducing device complexity and maintaining a constant awareness of how algorithms shape human psychology.