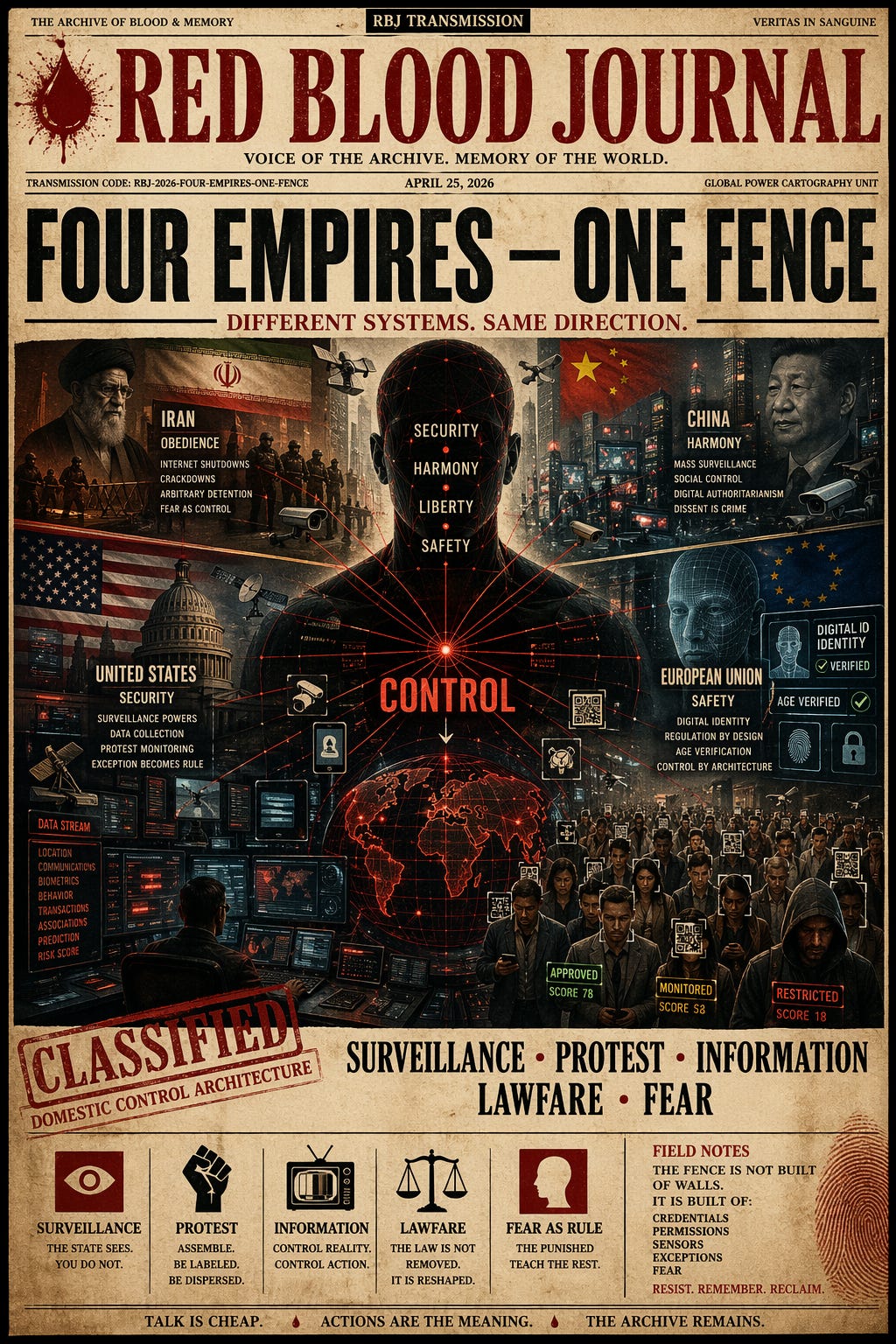
🩸 RED BLOOD JOURNAL TRANSMISSION
Archive: The Archive of Blood & Memory
Transmission Code: RBJ-2026-FOUR-EMPIRES-ONE-FENCE
Classification: Comparative Power Systems / Domestic Control Architecture
Desk: Global Power Cartography Unit
Status: Active Transmission
PROLOGUE — TALK IS CHEAP. RULE IS WHAT IS DONE.
Every state speaks a moral language.
Iran speaks of order, faith, and national security.
China speaks of harmony, stability, and anti-subversion.
The United States speaks of liberty, safety, and counterterrorism.
The European Union speaks of rights, safety, regulation, and democratic protection.
But states do not reveal themselves by slogans. They reveal themselves by what they build, what they monitor, what they punish, and what they normalize.
And when these four systems are compared by action rather than rhetoric, a hard pattern emerges:
They are not identical regimes.
They do not use equal force.
They do not operate under equal legal restraint.
But they keep reaching for the same governing instruments:
surveillance, identity, traceability, platform control, protest management, and emergency-style exceptions in law.
This is the sharper reading:
The elite classes of all four systems appear to be testing different versions of the same fence.
SECTION I — SURVEILLANCE: THE STATE WANTS TO SEE BEFORE IT STRIKES
Iran
In January 2026, the UN Fact-Finding Mission said Iran had to immediately restore internet and mobile access and end its violent crackdown on nationwide protest, indicating that communications control and repression were operating together. The Human Rights Council also renewed scrutiny over arbitrary detention, enforced disappearance, torture, and abuse against peaceful protesters.
China
China continues to expand surveillance-heavy governance through censorship, monitoring of religion, suppression of lawyers and dissidents, and broad state security control. Human Rights Watch and Freedom House describe a system in which legal counsel, religion, speech, and civic action are subordinated to state priorities.
United States
In the US, the form is different, but the architecture is still recognizable. Section 702 was temporarily extended again in April 2026, preserving a surveillance authority that critics say permits warrantless collection that can sweep in Americans’ communications. Civil-liberties groups continue to warn about secret interpretations, backdoor queries, facial recognition misuse, license-plate tracking, and protest surveillance.
European Union
The EU presents itself as rights-protective, and in many ways it is more rights-conscious than the other three. But it is also building a denser digital governance layer: the AI Act, age-verification systems, and the EU Digital Identity Wallet. Civil-liberties groups warn that these systems can drift toward tracking, compelled identification, and broader data linkage if safeguards fail or if the scope expands over time.
The common action
The common action is simple:
Each system wants more visibility into the population than the population has into the system.
That is the first fence.
SECTION II — PROTEST: WHEN CITIZENS MOVE, THE STATE REDEFINES THE MOVEMENT AS A THREAT
Iran
Iran’s response to protest remains the most openly violent of the four. UN bodies have documented extrajudicial killings, arbitrary arrests, incommunicado detention, torture, and severe violence against peaceful protesters.
China
China handles protest and dissent through preemption, detention, censorship, disappearance, legal intimidation, and coordinated pressure on social, religious, and legal networks. The goal is not merely to disperse protest but to make organization itself dangerous.
United States
In the US, protest remains constitutionally protected, which is a major structural difference. But protection on paper does not erase aggressive policing, aerial monitoring, facial-recognition misuse, and intelligence-style data collection around public assembly. Civil-liberties groups have documented surveillance of racial-justice protesters and raised alarms about broader federal-local enforcement concentration.
European Union
Across Europe, watchdogs and journalists’ groups report a pattern of protest restrictions, hostile policing, spyware fears, pressure on journalists, and shrinking civic space in multiple member states. The EU center may speak the language of democratic values while several member states operationalize the language of control.
The common action
When citizens gather, states frequently shift vocabulary:
Not assembly, but disorder.
Not dissent, but extremism.
Not grievance, but risk.
That semantic move gives the state permission to tighten the fence. This is an inference from the way the four systems justify interventions, not a direct quote from any one source.
SECTION III — INFORMATION CONTROL: HE WHO DEFINES THE REALITY DEFINES THE LIMITS OF ACTION
Iran
Iran uses internet shutdowns and mobile restrictions during unrest, which human-rights investigators explicitly linked to the violent crackdown and concealment of abuses.
China
China operates the most mature system of state-directed information management among the four: censorship, ideological conformity, platform control, religious control, and suppression of independent lawyers and journalists.
United States
The US does not operate a centralized censorship regime like China or Iran. That distinction matters. But US governance still includes powerful pressure points: intelligence secrecy, hidden legal interpretations, corporate-state information pipelines, and surveillance systems that can chill speech without formally banning it.
European Union
The EU is more conflicted than the others because it contains both rights-protective and rights-restrictive tendencies. On one side, the European Media Freedom Act is designed to protect editorial independence and journalistic sources against spyware. On the other, digital regulation, age-gating, and surveillance-expanding proposals continue to raise concerns from rights groups about online monitoring and restrictions on anonymity.
The common action
All four systems compete to control not only the citizen’s body in public space, but also the citizen’s narrative horizon:
What can be seen.
What can be verified.
What can be shared.
What can be said without cost.
SECTION IV — LAWFARE: THE LAW IS NOT REMOVED. IT IS RE-SHAPED INTO A WEAPON
The strongest modern systems do not always abolish law.
They weaponize legality.
Iran
Security courts, arbitrary detention, and prosecution of protesters convert repression into procedure.
China
China uses vague national-security and public-order frameworks, along with extrajudicial pressure and constrained legal counsel, to turn law into an arm of discipline.
United States
The US legal shell is more contested and adversarial, but the pattern remains: emergency powers, secret surveillance interpretations, broad intelligence authorities, immigration-enforcement expansion, and technologically assisted policing all demonstrate how exceptional authority can persist through legal form.
European Union
The EU legal model is more procedural and rights-aware, but it is also normalizing union-wide digital architecture: AI regulation, identity wallets, age verification, and rules that can widen institutional leverage over access, identity, and traceability. At the same time, EU watchdogs document rule-of-law backsliding in multiple member states, meaning the tools may outlast the liberal rhetoric that introduced them.
The common action
Lawfare is the art of making coercion look administrative.
Not “submit,” but “comply.”
Not “show your papers,” but “verify.”
Not “be watched,” but “be kept safe.”
That pattern is an inference drawn from the way official systems frame digital identity, age verification, surveillance, and security powers across jurisdictions.
SECTION V — FEAR AS RULE: MOST REGIMES DO NOT NEED TOTAL FORCE. THEY NEED PREDICTABLE CONSEQUENCES.
Fear is cheapest when it becomes ambient.
Iran shows what open terror looks like.
China shows what permanent disciplined conformity looks like.
The US shows how liberty can coexist with a security apparatus that citizens are told to trust but cannot fully see.
The EU shows how managerial liberalism can build tools that, under less liberal hands, become quiet instruments of exclusion and tracking.
The systems differ sharply in brutality and legal restraint. That difference is real and should not be blurred. But all four still teach the same civic lesson:
stay legible, stay calm, stay within the permitted channel, and the machine may leave you alone.
That is how the fence becomes internal. This concluding formulation is interpretive, but it is supported by the documented growth of surveillance, protest control, and identity-linked governance across the four jurisdictions.
ANNEX A — HOW THE ELITE TESTS THE FENCE
Across the four systems, the testing pattern appears to move in stages:
Stage 1: Declare a danger.
Terrorism, separatism, riots, extremism, disinformation, child safety, foreign interference, cybercrime, irregular migration.
Stage 2: Introduce a narrow tool.
Temporary surveillance power, emergency restrictions, targeted age checks, a specific digital ID function, limited content controls.
Stage 3: Normalize the infrastructure.
Databases connect. Platforms comply. ID systems expand. Police gain access. Private firms integrate.
Stage 4: Expand by exception.
The tool remains, but the use case widens. A child-safety tool becomes an identity precedent. A foreign-intelligence tool reaches domestic communications. A public-order system becomes a protest-management layer.
Stage 5: The citizen lives inside the system rather than merely under it.
This final step is most visible today in the EU’s digital-wallet buildout, China’s deep social and political monitoring, Iran’s communications repression, and the US fusion of intelligence, data brokerage, policing, and platform-adjacent surveillance. The degree differs, but the trajectory rhymes. This is an inference based on the cited measures, not a single officially declared joint plan.
ANNEX B — WHERE AND WHEN THEY BEGIN TO COME TOGETHER
There is no evidence in the sources of a single formal meeting where Iran, China, the US, and the EU openly agreed to build one planetary domestic-control grid together.
But there is evidence of convergence.
They come together functionally, not ceremonially.
They come together:
when identity becomes digital and portable, as in the EU wallet model due by the end of 2026, with age-verification infrastructure already declared ready in April 2026;
when surveillance powers persist through “temporary” renewal, as with the US Section 702 extension signed on April 18, 2026;
when protest and communications controls are fused, as seen in Iran’s January 2026 blackout-and-crackdown pattern;
when law, party power, and technical monitoring operate as one discipline system, as documented in China through continuing repression of lawyers, believers, and dissenters.
So when do they come together?
In this decade, through parallel buildout.
Most visibly in the mid-2020s, as digital identity, AI governance, age verification, cross-platform monitoring, and emergency surveillance authorities mature across jurisdictions.
So where do they come together?
Not in one capital.
In the infrastructure layer:
telecom systems
identity wallets
border and immigration databases
AI-assisted policing and verification
platform moderation and access control
government-corporate data cooperation
That is where the uniform system begins:
not as one flag, but as one logic.
CONCLUSION — FOUR LANGUAGES, ONE DIRECTION
Iran says obedience.
China says harmony.
The US says security.
The EU says safety and trust.
But beneath the language, the state impulse converges:
identify the citizen, map the citizen, classify the citizen, regulate the citizen, and condition the citizen to remain inside the approved lane.
Talking is cheap.
Actions are the meaning.
And the action pattern says this:
The future fence is not merely built of walls.
It is built of credentials, permissions, sensors, exceptions, and fear.
🕸️The Architecture of Global Control
Apr 20, 2026
This text analyzes how Iran, China, the United States, and the European Union are converging toward a shared architecture of social and digital control.
While their political ideologies and levels of transparency differ, the source argues that all four powers are adopting similar instruments of surveillance, identity tracking, and protest management.
The narrative suggests that these states prioritize population visibility and narrative control over genuine civil liberties, often redefining dissent as a threat to national security.
By implementing digital identity wallets, expanded surveillance authorities, and automated policing, these regimes create a “fence” that conditions citizens to remain within approved boundaries.
Ultimately, the document claims that despite their unique moral justifications, these global powers are building a unified logic of technological and legal restraint to ensure predictable public behavior.