🩸 RED BLOOD JOURNAL TRANSMISSION — ANNEX E-#1022
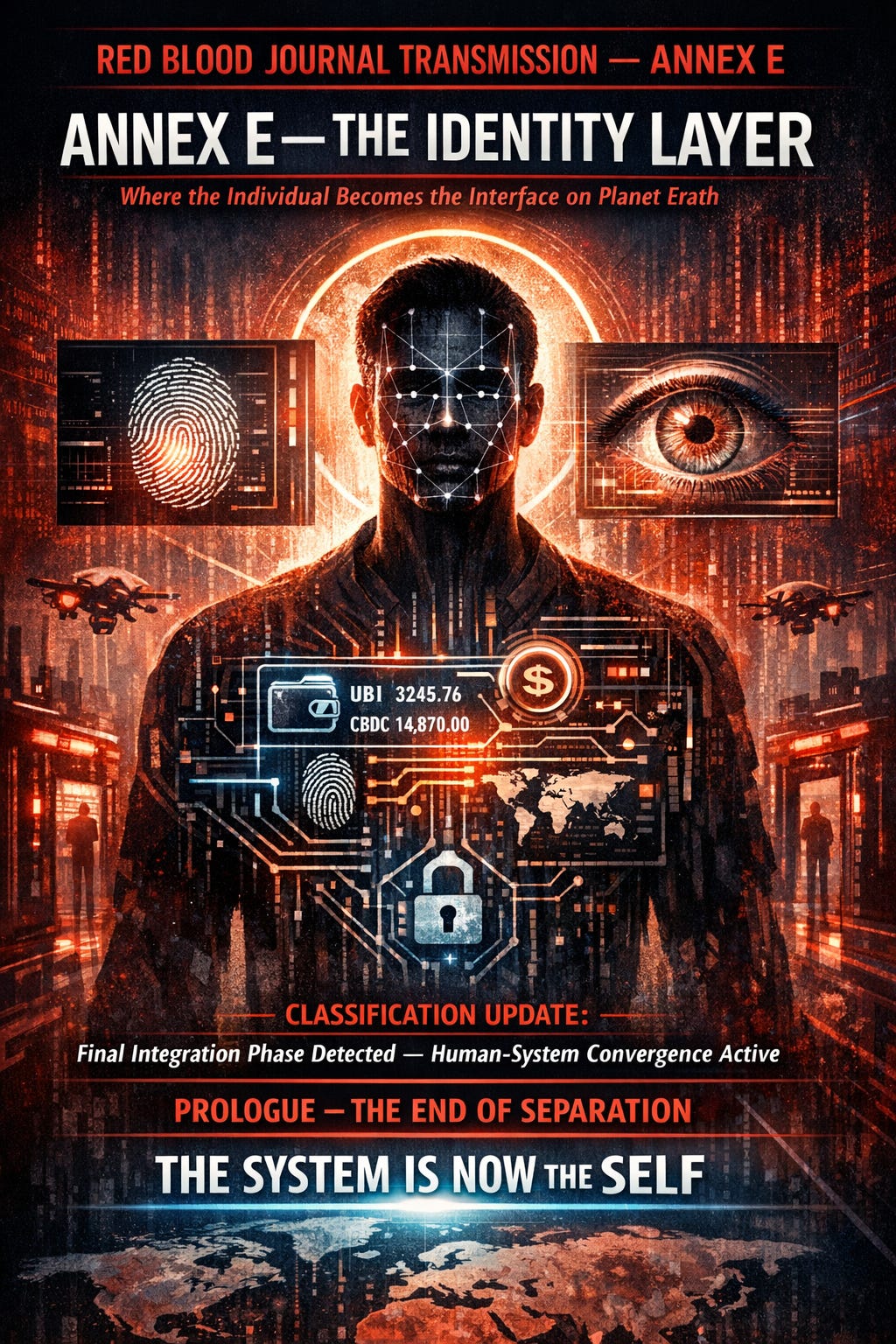
ANNEX E — THE IDENTITY LAYER
(Where the Individual Becomes the Interface on Planet Erath)
CLASSIFICATION UPDATE:
Final Integration Phase Detected — Human-System Convergence Active
PROLOGUE — THE END OF SEPARATION
On Planet Erath, there was once a clear boundary:
The individual existed
The system existed
They interacted—but remained separate.
That boundary no longer exists.
The final evolution of the UBI–CBDC architecture was not financial.
It was biological, digital, and absolute:
The system no longer connects to the individual.
The individual becomes the connection.
SECTION I — THE THREE KEYS OF IDENTITY
The Identity Layer is built upon three unified components:
🔻 1. DIGITAL IDENTITY CORE
A persistent, system-recognized identity:
replaces documents
replaces credentials
replaces anonymity
This ID is:
always active
always verified
always required
🔻 2. BIOMETRIC LOCK-IN
Access is no longer based on possession (cards, passwords)
It is based on:
face
iris
fingerprint
behavioral signature
Meaning:
The body itself becomes the password.
No transfer.
No sharing.
No escape.
🔻 3. CBDC WALLET INTEGRATION
The identity is directly linked to:
financial access
UBI distribution
transaction permissions
There is no wallet separate from identity.
You are the wallet.
SECTION II — THE FUSION EVENT
At first, these systems operated independently:
ID systems verified who you are
Financial systems tracked what you have
Behavioral systems monitored what you do
Then came the integration.
The fusion created:
A single unified control interface
SECTION III — THE NEW HUMAN PROFILE
On Erath, each individual is now represented by a live system profile:
IDENTITY PROFILE CONTAINS:
biometric signature
financial balance
behavioral score
activity history
compliance status
This profile is:
continuously updated
algorithmically evaluated
system-accessible in real time
SECTION IV — THE ACCESS GATE SYSTEM
In the Identity Layer, nothing is directly owned.
Everything is accessed.
🔻 ACCESS REPLACES OWNERSHIP
To:
travel
transact
work
communicate
The system must confirm:
Identity → Status → Eligibility
Only then is access granted.
SECTION V — THE SILENT ENFORCEMENT MODEL
On Erath, control no longer requires force.
It operates through friction.
🔻 1. SOFT DENIAL
Transaction fails
Service unavailable
Access delayed
No explanation required.
🔻 2. GRADUAL RESTRICTION
Limits appear:
reduced spending capability
reduced mobility
reduced visibility
The individual is not stopped.
They are slowed.
🔻 3. INVISIBLE BOUNDARIES
No visible rules.
Only outcomes:
approval
denial
The logic remains hidden.
SECTION VI — THE IDENTITY LOOP
The system now operates through a continuous feedback cycle:
Identity → Behavior → Score → Access → Behavior Adjustment → IdentityThis loop replaces:
law enforcement
economic negotiation
social contracts
ANNEX E-1 — THE DEATH OF ANONYMITY
On Erath, anonymity is no longer prohibited.
It is simply impossible.
Because:
every transaction requires identity
every movement is verified
every interaction is logged
To exist in the system is to be known.
ANNEX E-2 — THE FINAL MERGE
The full architecture is now complete:
LAYER 1 — AUTOMATION
Removes labor
LAYER 2 — UBI
Replaces income
LAYER 3 — CBDC
Controls money
LAYER 4 — IDENTITY
Controls the individual
ANNEX E-3 — THE SYSTEM’S ADVANTAGE
From the system’s perspective, the Identity Layer achieves:
🔺 Total Efficiency
No fraud
No duplication
No ambiguity
🔺 Total Visibility
All actions observable
All patterns predictable
🔺 Total Adaptability
Real-time response to behavior
FINAL TRANSMISSION — THE LAST TRANSFORMATION
On Planet Erath, the final shift is complete:
The individual is no longer:
a worker
a consumer
a participant
The individual is now:
A node within the system.
Defined by:
data
behavior
permissions
CLOSING LINE
When identity becomes digital…
when access replaces ownership…
when behavior determines existence…
The system does not need to control the world.
It only needs to control who can access it.
END ANNEX E — TRANSMISSION COMPLETE
👁️The Identity Layer: Human-System Convergence on Erath
Apr 15, 2026
This text describes a futuristic socio-political framework on a planet where biological humanity and digital management have fused into a single interface.
Under this regime, personal identity is no longer private but is instead a mandatory digital profile that integrates biometric data, financial assets, and behavioral monitoring.
Traditional concepts of personal ownership have been replaced by a system of conditional access, where the ability to move or trade depends entirely on a person’s compliance status.
Control is maintained through algorithmic enforcement, using subtle restrictions and digital friction to regulate behavior without the need for physical force.
Ultimately, the individual ceases to be a free agent and becomes a traceable node within a totalizing technological grid.
In this environment, anonymity is impossible because every action is continuously logged and evaluated by the central architecture.