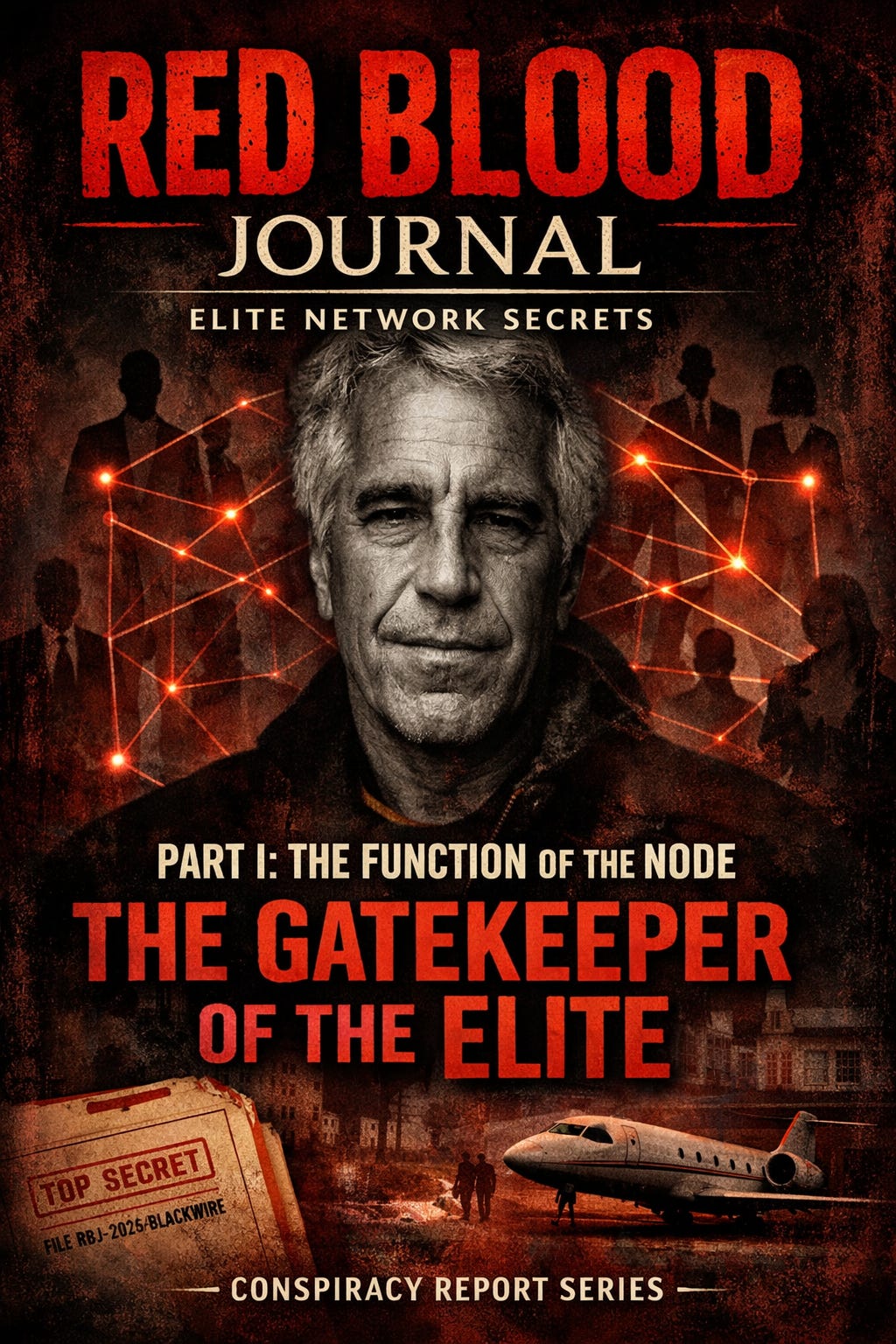
🩸 RED BLOOD JOURNAL TRANSMISSION
T#: RBJ-2026-BLACKWIRE-EPSTEIN-I
Classification: Network Penetration Asset Theory / Elite Compromise Infrastructure / Sovereign Influence Architecture
Desk: Counterintelligence Mythology Division — Archive of Blood & Signal
Volume: I of V
Status: Active Reconstruction Phase
PART I — THE FUNCTION OF THE NODE
PROLOGUE — MEN LIKE EPSTEIN ARE NEVER THE CENTER. THEY ARE THE CONNECTOR.
History does not remember the wire.
It remembers the current.
Jeffrey Epstein was not powerful because of his money.
He was powerful because of his position.
He existed at the precise intersection between access and secrecy.
Not as king.
Not as servant.
But as something far more structurally valuable:
An interface.
The released FBI files, the deleted-page sheets, the exemption code patterns, and the investigative architecture do not describe the profile of a conventional criminal enterprise alone.
They describe the profile of a network node whose primary function was not simply exploitation—
—but access mediation.
SECTION I — THE STRUCTURE OF ACCESS CONTROL
The FBI Vault records show large-scale page deletions protected under exemption code b7D.
This exemption protects confidential human sources.
This is the most revealing structural signal in the entire archive.
Because confidential sources do not emerge randomly.
They exist inside networks.
Which means investigators encountered individuals embedded within Epstein’s operational environment who possessed privileged internal knowledge.
This reveals an essential truth:
Epstein’s operation was not isolated.
It was integrated.
Not at the margins.
At the center.
SECTION II — THE REAL CURRENCY WAS NOT MONEY
Money is transactional.
Access is strategic.
Epstein’s most unusual characteristic was not wealth accumulation.
It was access distribution.
He operated as a broker between worlds normally separated by invisible institutional barriers:
Finance
Politics
Academia
Corporate leadership
Scientific research
International social elites
This type of cross-domain access brokerage serves a known structural function.
It allows the mapping of influence pathways.
Not in theory.
In practice.
SECTION III — THE COMPROMISE VECTOR
The FBI’s heavy redaction of entire investigative chains strongly suggests investigators encountered sensitive relational pathways.
Not just individual acts.
Patterns of interaction.
Because in influence architecture, compromise is not always immediate.
It is stored.
Catalogued.
Activated when necessary.
Not for punishment.
For control.
The existence of large deleted-page blocks clustered around investigative expansion phases indicates investigators likely traced chains beyond Epstein himself.
Chains that did not begin with him.
And did not end with him.
SECTION IV — THE ROLE OF THE SOCIAL ENGINEER
Epstein’s publicly visible function was financier.
His structurally inferred function was gatekeeper.
He created environments where individuals of strategic importance interacted in private contexts.
These environments had several characteristics:
Isolation from institutional oversight
Controlled access points
Predictable guest circulation
Psychological familiarity and trust development
This is how long-term influence infrastructure is built.
Not through coercion.
Through voluntary exposure.
Once exposure exists, leverage exists.
Not always used.
But always available.
SECTION V — WHY THE FILES ARE STRUCTURALLY OPAQUE
The FBI’s Deleted Page Information Sheets show hundreds of withheld pages in single investigative segments.
This pattern does not resemble the protection of isolated victims alone.
It resembles the protection of relational architecture.
Because when you remove the identity of a victim, you redact a name.
When you remove the identity of a confidential source, you redact chains.
Entire investigative logic trees must be obscured.
Not because the event is unknown.
But because the network is known.
SECTION VI — THE MOST LIKELY FUNCTION: THE NETWORK MAPPER
From the conspiracy analysis viewpoint, the most plausible structural role Epstein served was this:
He functioned as a network mapper and access broker.
Not necessarily the ultimate authority.
But the interface layer.
His duties likely included:
Identifying individuals of influence
Facilitating private access environments
Maintaining relational continuity between elites
Tracking behavioral vulnerabilities
Maintaining loyalty networks through social leverage
This role does not require ideological alignment.
It requires proximity.
And discretion.
SECTION VII — WHY SUCH ASSETS EXIST
Influence networks do not operate solely through institutions.
They operate through individuals positioned at network intersections.
These individuals perform three critical functions:
Access creation
Information acquisition
Influence preservation
They do not govern openly.
They enable governance behind the visible structure.
They are not the rulers.
They are the wiring.
SECTION VIII — EPSTEIN AS A FUNCTION, NOT A PERSON
The FBI file architecture reveals an investigation into a man.
The redaction architecture reveals an investigation into a system.
The difference between those two is the difference between crime and infrastructure.
Epstein’s personal actions triggered the investigation.
But the structural sensitivity of the files suggests investigators encountered something larger than individual misconduct.
They encountered a network topology.
And topology cannot be prosecuted.
Only nodes can.
TERMINAL ASSESSMENT — VOLUME I
From a conspiracy analysis perspective, the most plausible interpretation of Epstein’s role is not that of an isolated criminal, but that of a strategic access node embedded within elite relational infrastructure.
His power did not come from ownership.
It came from position.
He was not the apex.
He was the interface.
Which is why his removal did not collapse the network.
Because networks do not depend on individuals.
They depend on structure.
END TRANSMISSION — VOLUME I
🕸️The Epstein Interface:
Architecture of Elite Network Control
The provided text characterizes Jeffrey Epstein not as an independent criminal, but as a strategic interface designed to facilitate and monitor elite networks.
By analyzing FBI redaction patterns and investigative gaps, the source argues that Epstein functioned as a human network mapper who bridged the worlds of politics, science, and finance.
His primary value lay in access mediation, creating private environments where influential figures could be observed and potentially compromised.
The heavy use of confidential source exemptions in government files suggests that investigators uncovered a broad system of influence rather than just individual misconduct.
Ultimately, the document asserts that Epstein was a functional node within a permanent architecture of control that exists independently of any single person.