🩸 RED BLOOD JOURNAL TRANSMISSION #1078
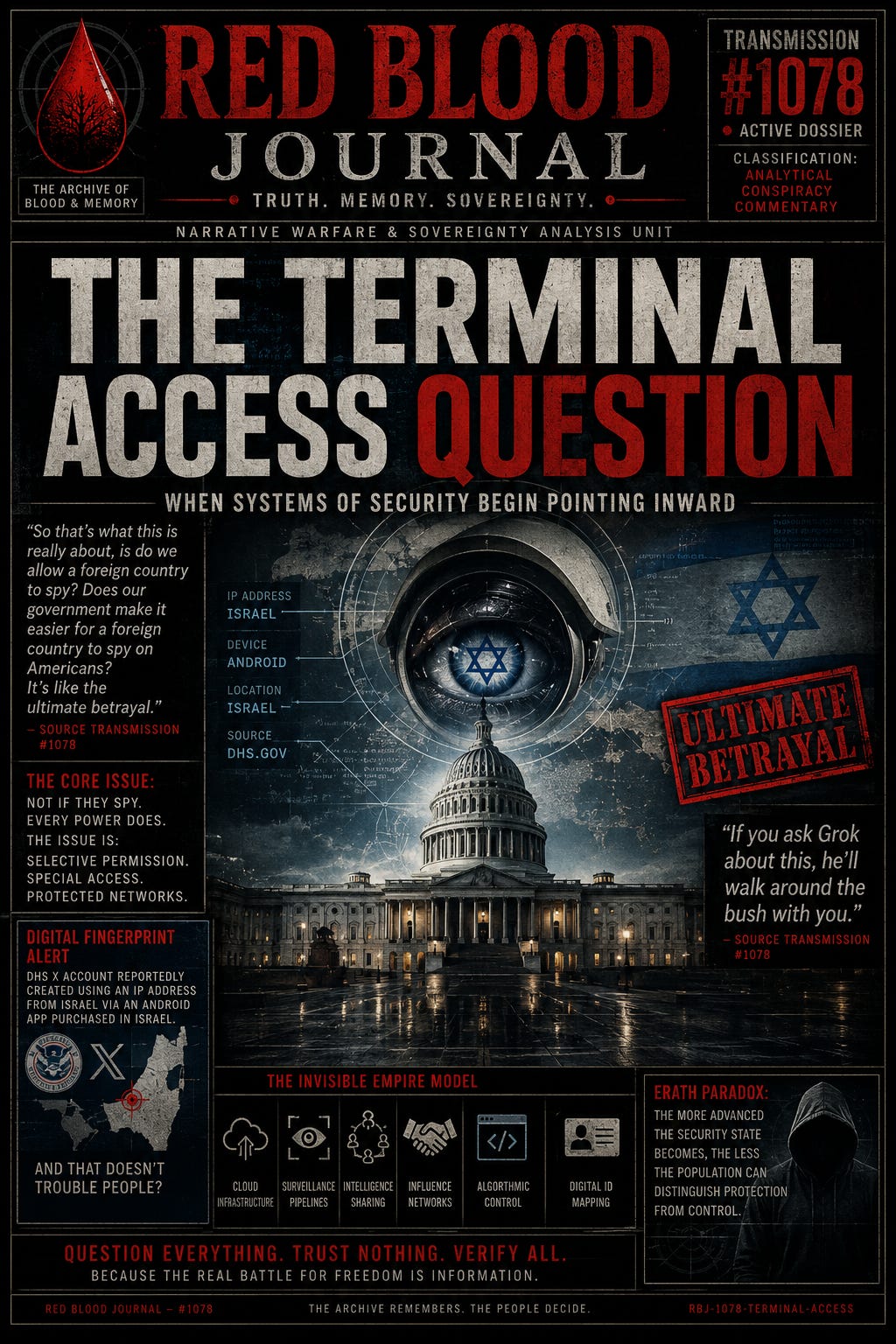
“THE TERMINAL ACCESS QUESTION”
When Systems of Security Begin Pointing Inward
Archive: The Archive of Blood & Memory
Division: Narrative Warfare & Sovereignty Analysis Unit
Classification: Analytical Conspiracy Commentary
Transmission Code: RBJ-1078-TERMINAL-ACCESS
Status: Active Transmission
Desk: Counterintelligence Signal Mapping Wing
PROLOGUE — THE QUESTION BEHIND THE QUESTION
Sometimes the most dangerous sentence is not an accusation.
It is a question.
“Do we allow a foreign country to spy?
Does our government make it easier for a foreign country to spy on Americans?”
On the planet Erath, entire civilizations are conditioned to argue only about surface politics while never examining the architecture underneath the stage.
The masses are trained to focus on personalities.
The real operators focus on infrastructure.
Who owns the platforms?
Who monitors the traffic?
Who writes the interpretation manuals?
Who controls the emergency switches?
Who receives privileged access in the name of “security cooperation”?
That is where the real transmission begins.
SECTION I — SECURITY OR SHARED ACCESS?
Modern empires no longer require visible occupation.
They require integration.
The Erath model evolved beyond traditional espionage decades ago.
The new model is partnership intelligence architecture:
Shared databases
Shared cyber monitoring
Shared “counter-terrorism” frameworks
Shared surveillance pipelines
Shared AI analysis systems
Shared telecommunications interception
Under this structure, the line between:
ally,
contractor,
intelligence proxy,
and foreign influence network
becomes increasingly blurred.
The public is told:
“This is for your protection.”
But the deeper question becomes:
Who exactly is being protected?
And from whom?
SECTION II — THE DIGITAL FINGERPRINT PROBLEM
One statement inside the source material acts like a tiny crack in a massive wall:
“The DHS account showed Israel… the US Department of Homeland Security’s X account was set up using an IP address from Israel…”
Whether fully verified, partially misunderstood, or operationally explainable, the existence of such claims reveals something deeper:
Modern citizens no longer trust institutional transparency.
Why?
Because Erath’s systems repeatedly classify critical operational details while demanding blind public trust.
The result:
secrecy upward,
visibility downward.
Citizens are monitored continuously.
Governments increasingly operate behind classification barriers.
This inversion creates a psychological fracture:
the population begins assuming hidden layers exist behind every anomaly.
And sometimes they do.
SECTION III — THE “ALLY EXCEPTION”
On Erath, certain nations eventually transcend the normal rules applied to everyone else.
Criticism becomes dangerous.
Questioning becomes taboo.
Investigations become politically radioactive.
That is when a relationship moves beyond diplomacy and enters protected-network status.
The transmission argues that the true issue is not merely spying itself.
Every major power spies.
The deeper concern is selective permission.
When populations believe:
one foreign actor receives special immunity,
while domestic citizens receive aggressive scrutiny,
trust collapses.
And once trust collapses, every unexplained anomaly becomes interpreted as evidence of coordinated infiltration.
SECTION IV — THE INVISIBLE EMPIRE MODEL
The old empire occupied land.
The new empire occupies systems.
Not through flags.
Through:
software,
lobbying,
intelligence sharing,
cybersecurity firms,
data pipelines,
cloud infrastructure,
influence networks,
platform moderation channels,
and dependency architecture.
The public still imagines espionage as:
trench coats,
hidden cameras,
dead drops.
But on Erath, modern surveillance resembles:
algorithmic visibility control,
metadata harvesting,
behavioral prediction,
digital identity mapping,
and social graph analysis.
The citizen voluntarily carries the tracking device.
Then calls it freedom.
SECTION V — THE THEATER OF PLAUSIBLE DENIABILITY
The transmission source notes:
“If you ask Grok about this, he’ll walk around the bush with you.”
This reflects a growing public perception that modern information systems no longer answer directly.
Instead they:
soften,
redirect,
contextualize,
neutralize,
and de-risk narratives.
Not necessarily because every claim is true.
But because systems are increasingly optimized for stability management rather than raw transparency.
The result is a civilization trapped between:
institutional secrecy,
algorithmic mediation,
and collapsing public trust.
On Erath, this creates the perfect breeding ground for conspiracy ecosystems.
Because when people sense hidden architecture but cannot see its boundaries, they begin constructing maps in the dark.
ANNEX A — THE ERATH PARADOX
The paradox is simple:
The more advanced the security state becomes,
the less the population can distinguish:
protection,
partnership,
influence,
dependency,
and control.
Eventually citizens ask:
Who is actually operating the machine?
And once that question enters the bloodstream of a civilization, it never fully disappears.
FINAL TRANSMISSION
On the planet Erath, the greatest fear is no longer invasion from outside.
It is the possibility that the boundary between:
domestic governance,
foreign influence,
intelligence cooperation,
and corporate infrastructure
has already dissolved beyond public visibility.
And if the citizens cannot see where one system ends and another begins…
then perhaps the real power structure was never national at all.
👁️ The Architecture of Inward Security
May 7, 2026
This text analyzes the blurred boundaries between domestic governance, corporate infrastructure, and foreign influence within modern digital systems.
It argues that traditional forms of conquest have been replaced by an invisible architecture of shared surveillance pipelines and integrated intelligence networks.
The narrative suggests that the public is often distracted by surface-level politics while global power players establish control through software, data harvesting, and selective access.
This deep level of systemic integration causes a total collapse of public trust, as citizens can no longer distinguish between genuine protection and foreign manipulation.
Ultimately, the source posits that the true ruling structures operate behind a veil of secrecy, making it impossible for the average person to identify who actually manages the mechanisms of state security.