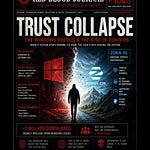
🩸 RED BLOOD JOURNAL TRANSMISSION
Division: Corporate Power Architecture Unit
Transmission Code: RBJ-CONSUMER-TRAP-APPLECARE-001
Classification: Contractual Control Systems / Soft Compliance Engineering
Archive: The Archive of Blood & Memory
How warranties destroy true ownership
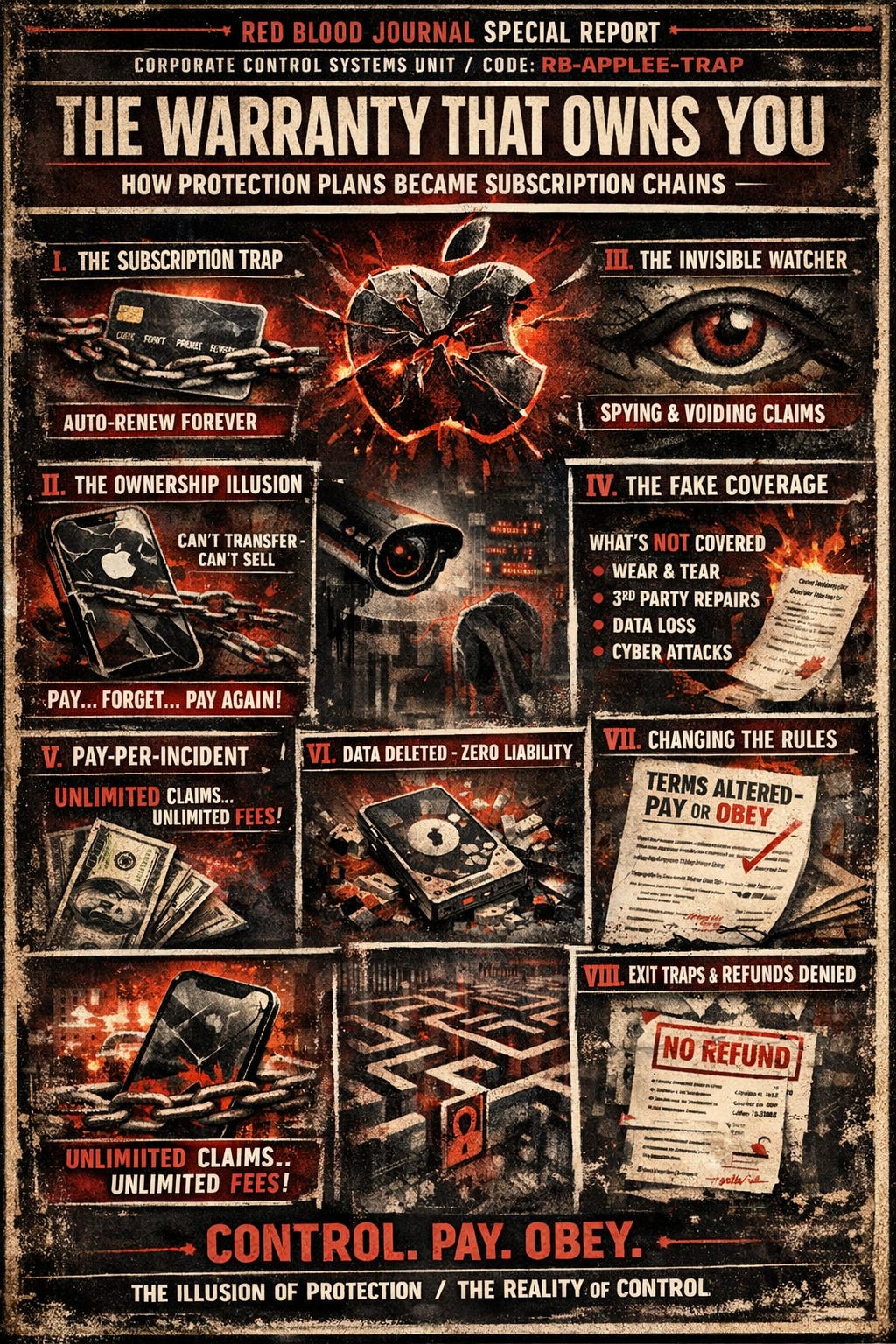
🍎 THE WARRANTY THAT OWNS YOU
How Protection Plans Became Subscription Chains
🪐 PROLOGUE — THE ILLUSION OF SAFETY
On the surface, it is presented as protection.
A shield.
A safety net.
A promise.
“You are covered.”
But on the deeper layer of Planet Erath…
Nothing is sold without a second purpose.
And sometimes, the thing sold as protection…
is actually a system of controlled dependency.
I — THE SUBSCRIPTION THAT NEVER ENDS
The first mechanism is not hidden.
It is simply normalized.
Automatic renewal.
Not once.
Not twice.
But indefinitely.
No friction.
No interruption.
No required re-consent.
Just a silent continuation of extraction.
🧠 RBJ INTERPRETATION:
This is not billing.
This is behavioral inertia weaponized.
The system does not rely on agreement —
it relies on forgetfulness.
A device is sold once.
The subscription can last longer than the device itself.
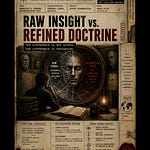
II — THE OWNERSHIP ILLUSION
You bought the device.
But the protection tied to it?
Not really yours.
It cannot follow the object.
It cannot follow the value.
It dies with the original buyer —
or worse, it stays behind… still charging.
🧠 RBJ INTERPRETATION:
Ownership has been split into layers:
Physical ownership → yours
Functional protection → controlled
Transferable value → restricted
This is how resale markets are quietly weakened.
Not by banning trade…
but by stripping value from the product after sale.
III — THE INVISIBLE WATCHER
Buried in the language:
“Apple has the right to monitor your service requests…”
A simple sentence.
But it reveals something deeper.
The system is not passive.
It observes behavior.
And it enforces compliance based on interpretation.
What counts as “commercial use”?
What counts as “private gain”?
The definitions are flexible.
The enforcement is not.
🧠 RBJ INTERPRETATION:
This is the transition from:
Service provider → behavior regulator
Violation does not mean penalty.
It means termination without refund.
Judge. Jury. Executioner.
All in one clause.
IV — THE COVERAGE THAT DOESN’T COVER
The promise:
“Accidental Damage Protection”
The reality:
Not wear and tear
Not cosmetic damage
Not “reckless” use (undefined)
Not third-party repair
Not environmental events
Not data loss
Not cyber incidents
The definition of “accident” becomes…
surgically narrow.
🧠 RBJ INTERPRETATION:
This is linguistic engineering.
The word “coverage” remains intact…
While the meaning is hollowed out from within.
V — THE PAY-TO-FAIL MODEL
Even when the system activates…
You still pay.
Every time.
Screen breaks → fee
Device damage → higher fee
Replacement → sometimes highest fee
“Unlimited claims”
With unlimited charges attached.
🧠 RBJ INTERPRETATION:
This is not insurance.
This is structured cost deferral.
You are not avoiding expense.
You are prepaying + postpaying simultaneously.
VI — THE DATA SACRIFICE CLAUSE
During service:
Everything is erased.
Everything.
And if something is lost?
That is your responsibility.
Even if the system caused it.
Even if the technician caused it.
🧠 RBJ INTERPRETATION:
In the digital age, data is identity.
And yet:
The contract assigns zero value to your data.
Only the hardware is protected.
The real asset is not.
VII — THE RULES THAT SHIFT UNDER YOUR FEET
The system can change itself.
At will.
With notice — yes.
But with a condition:
If you continue… you agree.
No signature required.
No new contract required.
Just continued existence in the system.
🧠 RBJ INTERPRETATION:
Consent is redefined as:
Failure to escape.
VIII — THE EXIT MAZE
Leaving the system is not impossible.
But it is… structured.
Refunds shrink over time
Timing determines eligibility
Chargebacks trigger penalties
Violations erase refunds entirely
And the most silent mechanism:
Trade in your device?
The plan disappears.
Automatically.
🧠 RBJ INTERPRETATION:
Entry is one click.
Exit is a procedural labyrinth.
IX — THE GEOGRAPHIC CAGE
Travel.
Move.
Relocate.
The system does not follow easily.
Service becomes restricted.
Costs increase.
Logistics become your burden.
🧠 RBJ INTERPRETATION:
Global product.
Localized control.
Mobility is allowed…
Until you need support.
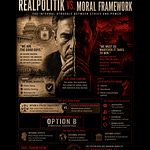
X — THE LEGAL FORTRESS
At the foundation:
Liability is capped.
Not at your loss.
Not at your damage.
But at what you paid.
Everything beyond that?
Not their responsibility.
🧠 RBJ INTERPRETATION:
This is the ultimate inversion:
Maximum control.
Minimum accountability.
🩸 FINAL ANALYSIS — THE SOFT CONTROL SYSTEM
This is not unique.
This is a template.
A pattern seen across:
Subscriptions
Extended warranties
Digital services
Platform ecosystems
The formula is consistent:
Promise protection
Introduce dependency
Limit real coverage
Automate payment
Restrict exit
Eliminate liability
🧠 RBJ CLOSING INTERPRETATION
On Planet Erath…
Control no longer arrives with force.
It arrives with:
Terms & Conditions
Checkboxes
Auto-renew toggles
No chains.
No guards.
Just agreements.
And the most effective system ever built is one where:
The subject believes…
They chose it.
🩸 ARCHIVE NOTE
The most powerful systems are not the ones that take freedom.
They are the ones that redefine what freedom looks like…
Until no one remembers the difference.
⛓️The Architectures of Digital Dependency:
The Illusion of Protection
The provided text critiques modern service contracts and protection plans, framing them as sophisticated tools for corporate dominance rather than genuine consumer safety.
By using automated renewals and complex procedural hurdles, companies exploit human psychology to ensure perpetual financial extraction.
The source argues that product ownership has been eroded, as manufacturers maintain strict control over device utility while simultaneously minimizing their own liability.
Through narrow definitions of coverage and high service fees, these systems create a dependency loop where users pay for the illusion of security.
Ultimately, the text warns that these digital ecosystems redefine freedom by trapping consumers in a labyrinth of invisible, yet binding, legal agreements.