🩸 Turnkey Tyranny — From “Human Intel” Hustle to Stellar Wind’s Paper Trail (Part II of IV)
🩸The Red Blood Journal Transmission
Turnkey Tyranny — From “Human Intel” Hustle to Stellar Wind’s Paper Trail (Part II of IV)
Source: JRE #1368 — Edward Snowden (2019)
Focus: How the human-intel hustle, industry–state cloud buildout, and an “accidental” dirty-word search led Snowden to the Inspector General report on Stellar Wind—and to the conclusion that policy was bent to fit power, not the law.
1) The Human Game: Cheap Stakes, Broken Lives
HUMINT vs. SIGINT. CIA leans on HUMINT—turning insiders at banks, telcos, and ministries; NSA dominates SIGINT—wires, packets, devices.
Snowden’s early disillusion: aggression outpacing value. Careers were advanced on low-stakes targets, even if the method wrecked civilians for crumbs of intel.
Lesson: skepticism accretes—from anomalies to pattern.
2) The Commercial State: Selling the Panopticon
Rotations: NSA Tokyo → CIA account (at Dell). As a young technical lead, Snowden pitched private-cloud systems to CIA chiefs.
Takeaway: Classified America is a market. Big Tech runs secret clouds for government; the real question in the room is:
“How much can we extract from the budget?”Result: A deep industry–state braid where contractors design the plumbing of power and then profit from its flow.
3) Hawaii, “No-Work Office,” and a Dangerous Curiosity
Reassigned to a forgotten corner: Office of Information Sharing (OIS).
Built Heartbeat: a cross-domain aggregator that bridged compartments, surfacing mission-relevant docs to each employee profile.
Side task: “dirty word searches”—automated queries across compartments, including above-Top-Secret caveats.
Then the hit: STLW — Stellar Wind.
4) Lifting the Floorboards: What “STLW” Unlocked
File traced to an NSA Inspector General draft brought by a visiting lawyer.
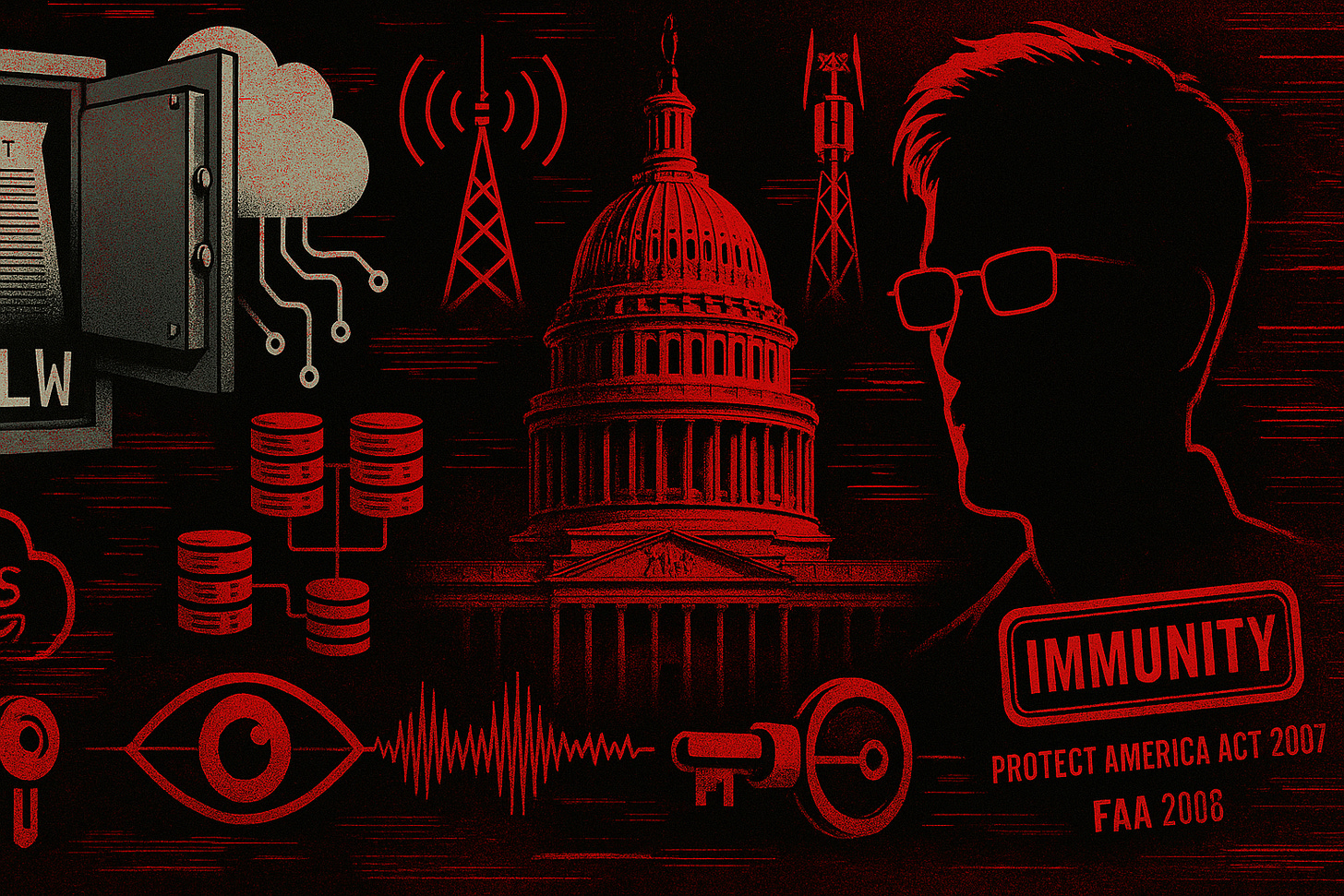
Stellar Wind = Bush-era warrantless wiretapping (mass domestic collection) born of secret Addington memos in Cheney’s orbit.
Media choreography: NYT sat on the story pre-election 2004; published Dec 2005 under pressure from Risen’s forthcoming book.
Damage control:
2007 Protect America Act → retroactive immunity for telcos that handed over your records on a presidential letterhead.
2008 FISA Amendments Act (FAA) → codified the dragnet with legal hoops rather than restraints, expanding authorities after the scandal.
Snowden’s realization: The IG draft named names and mapped a tick-tock where senior officials knew illegality yet continued at presidential request. Continuity of government trumped Constitutional constraint.
5) Overclassification: How Secrecy Manufactures Consent
In the IC, even lunch plans can be “classified.” Compartmentation keeps workers siloed and gagged.
Public “unclassified” reports were not redactions of the classified versions; they were entirely different documents—crafted to mislead Congress and the public.
This is the practical face of a “secret government”: secret law + secret policy + secret interpretations.
6) National Security vs. Public Safety
Snowden’s distinction: “National security” == state security. It often diverges from public safety and civil liberty.
Loyalty is only virtuous if tied to the common good; loyalty to bad programs does harm.
7) The Permanent Record Era
Phones + platforms = memory without mercy.
AT&T Hemisphere: long-tail call-detail retention (records of who/when/where, not necessarily content) stretching back decades; crossing AT&T’s network can still place you in the logbook.
Net effect: Citizens live naked before power, while power lives clothed in secrecy.
Pull-Quotes (Front-Page Ready)
“They didn’t make the agencies follow the law; they made the law follow the agencies.”
“Continuity of government outranked the Constitution.”
“A public report that isn’t the same document—it’s a deception strategy, not a redaction strategy.”
🩸RBJ Takeaways (Part II)
The Market Built the Machine: Surveillance capacity is outsourced, productized, and upsold.
Immunity Is the Tell: When Congress retroactively shields partners, you’re watching power laundering.
Secrecy Scales, Accountability Shrinks: Overclassification converts scandals into procedures.
Data Gravity Wins: Your metadata outlives your mistakes—and your rights, unless checked.
Practical Literacy (Do This)
Demand provenance: Whenever an “unclassified” report is cited, ask: Is it the same doc minus redactions—or a different doc?
Follow the authorizer: Was the authority statute, court order, or policy memo? If policy, it’s revocable by pen.
Map the contractor chain: Who builds, hosts, and maintains the systems behind the order?
Next in the Series (Part III Preview)
Pipes & Programs: From PRISM, Upstream, and XKEYSCORE to how FISA was stretched; the “proper channels” myth; and why metadata is often more dangerous than content.